- Forums
- Product Forums
- General Purpose MicrocontrollersGeneral Purpose Microcontrollers
- i.MX Forumsi.MX Forums
- QorIQ Processing PlatformsQorIQ Processing Platforms
- Identification and SecurityIdentification and Security
- Power ManagementPower Management
- Wireless ConnectivityWireless Connectivity
- RFID / NFCRFID / NFC
- Advanced AnalogAdvanced Analog
- Neural Processing UnitsNeural Processing Units
- MCX Microcontrollers
- S32G
- S32K
- S32V
- MPC5xxx
- Other NXP Products
- S12 / MagniV Microcontrollers
- Powertrain and Electrification Analog Drivers
- Sensors
- Vybrid Processors
- Digital Signal Controllers
- 8-bit Microcontrollers
- ColdFire/68K Microcontrollers and Processors
- PowerQUICC Processors
- OSBDM and TBDML
- S32M
- S32Z/E
-
- Solution Forums
- Software Forums
- MCUXpresso Software and ToolsMCUXpresso Software and Tools
- CodeWarriorCodeWarrior
- MQX Software SolutionsMQX Software Solutions
- Model-Based Design Toolbox (MBDT)Model-Based Design Toolbox (MBDT)
- FreeMASTER
- eIQ Machine Learning Software
- Embedded Software and Tools Clinic
- S32 SDK
- S32 Design Studio
- GUI Guider
- Zephyr Project
- Voice Technology
- Application Software Packs
- Secure Provisioning SDK (SPSDK)
- Processor Expert Software
- Generative AI & LLMs
-
- Topics
- Mobile Robotics - Drones and RoversMobile Robotics - Drones and Rovers
- NXP Training ContentNXP Training Content
- University ProgramsUniversity Programs
- Rapid IoT
- NXP Designs
- SafeAssure-Community
- OSS Security & Maintenance
- Using Our Community
-
- Cloud Lab Forums
-
- Knowledge Bases
- ARM Microcontrollers
- i.MX Processors
- Identification and Security
- Model-Based Design Toolbox (MBDT)
- QorIQ Processing Platforms
- S32 Automotive Processing Platform
- Wireless Connectivity
- CodeWarrior
- MCUXpresso Suite of Software and Tools
- MQX Software Solutions
- RFID / NFC
- Advanced Analog
- Neural Processing Units
-
- NXP Tech Blogs
- Home
- :
- Wireless Connectivity
- :
- Wireless Connectivity Knowledge Base
- :
- Use the USB-KW41 + Wireshark for Thread Sniffing
Use the USB-KW41 + Wireshark for Thread Sniffing
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Options
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Use the USB-KW41 + Wireshark for Thread Sniffing
Use the USB-KW41 + Wireshark for Thread Sniffing
802.15.4 wireless sniffers like the USB-KW41Z are capable of capturing over-the-air traffic. The captured packets are passed to a network protocol decoder like Wireshark over a network interface tunnel built by the Kinetis Protocol Analyzer.
Hardware
One USB-KW41Z preloaded with sniffer firmware ( instructions found at www.nxp.com/usb-kw41z )
Software Download & Install
Thread Wireshark from wireshark.org which is an open-source network protocol analyzer capable of debugging over the air communication between Thread devices.
Kinetis Protocol Analyzer is a software that provides a bridge between the USB-KW41 and Wireshark.
Wireshark Configuration
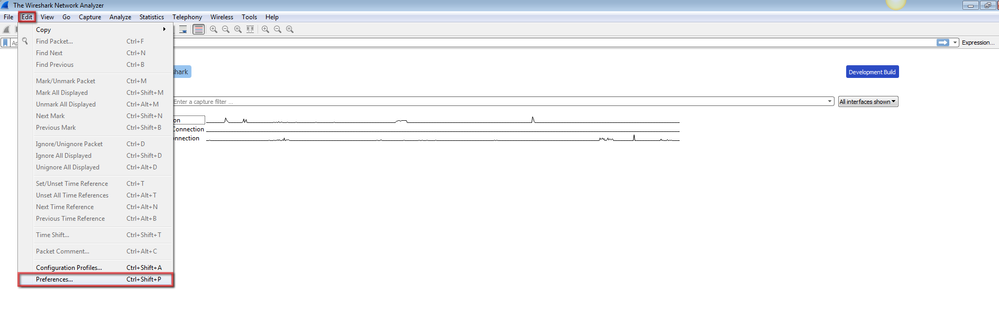
- Open Wireshark from the Program Files
- Click Edit and select Preferences
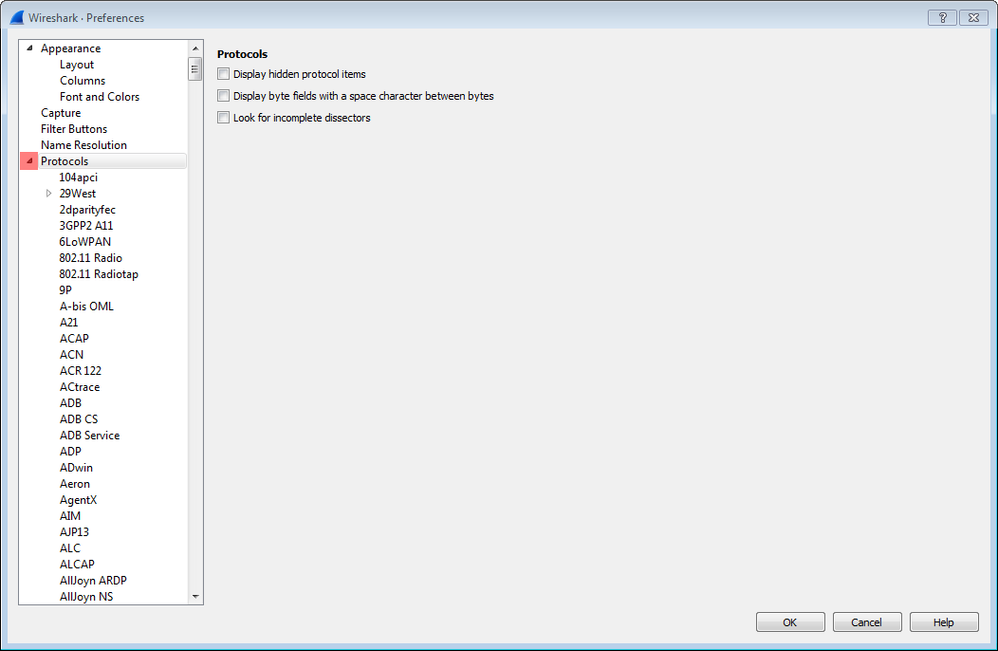
- Click Protocols to expand a list of protocols
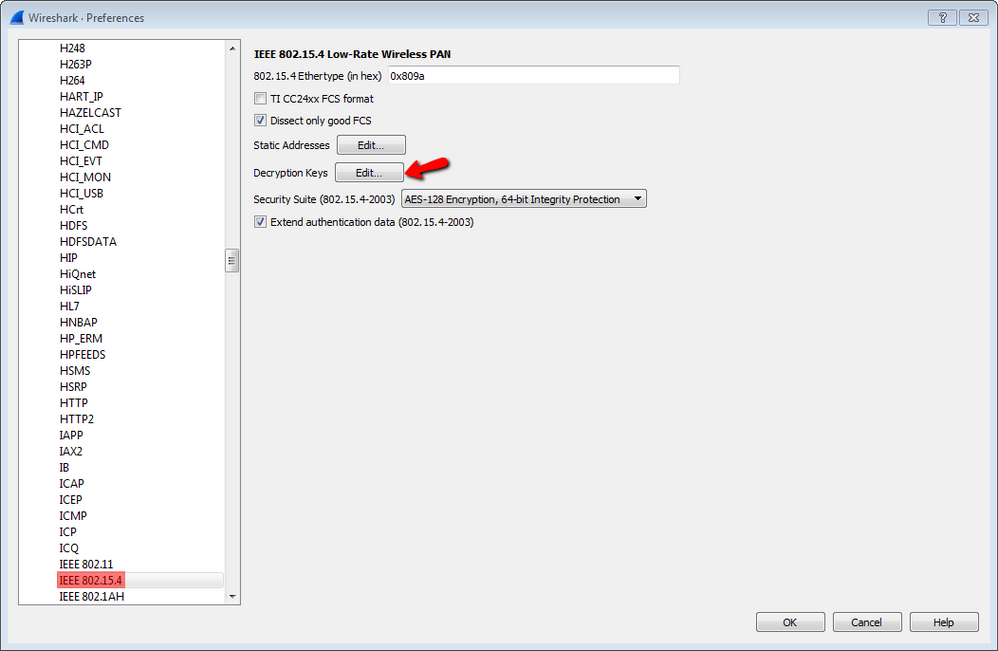
- Select IEEE 802.15.4, click the Decryption Keys Edit... button
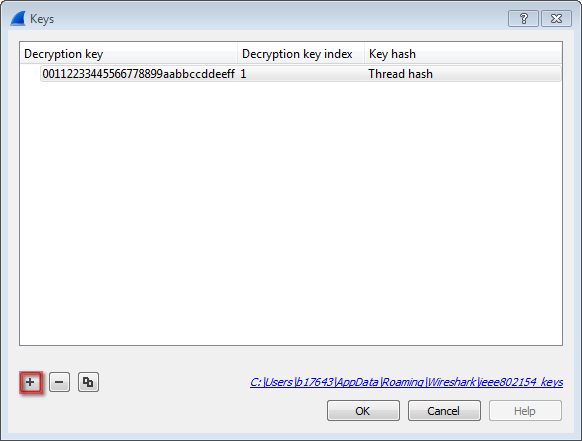
- Create a new key entry by pressing the plus button, then set the following values and click OK
Decryption key = 00112233445566778899aabbccddeeff
Decryption key index = 1
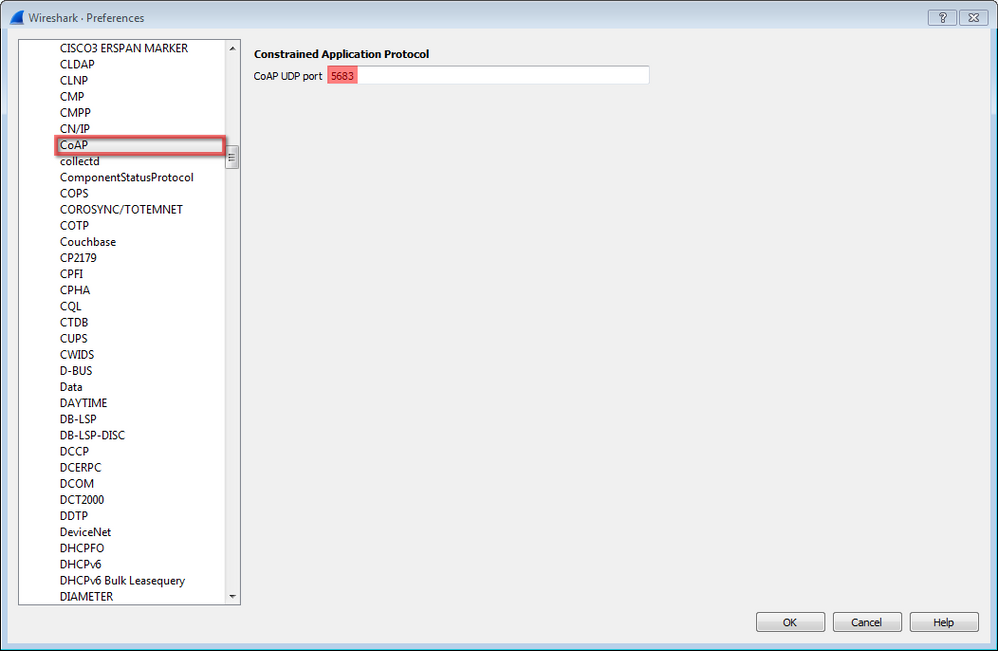
Key hash = Thread hash - Find CoAP and configure it with CoAP UDP port number = 5683
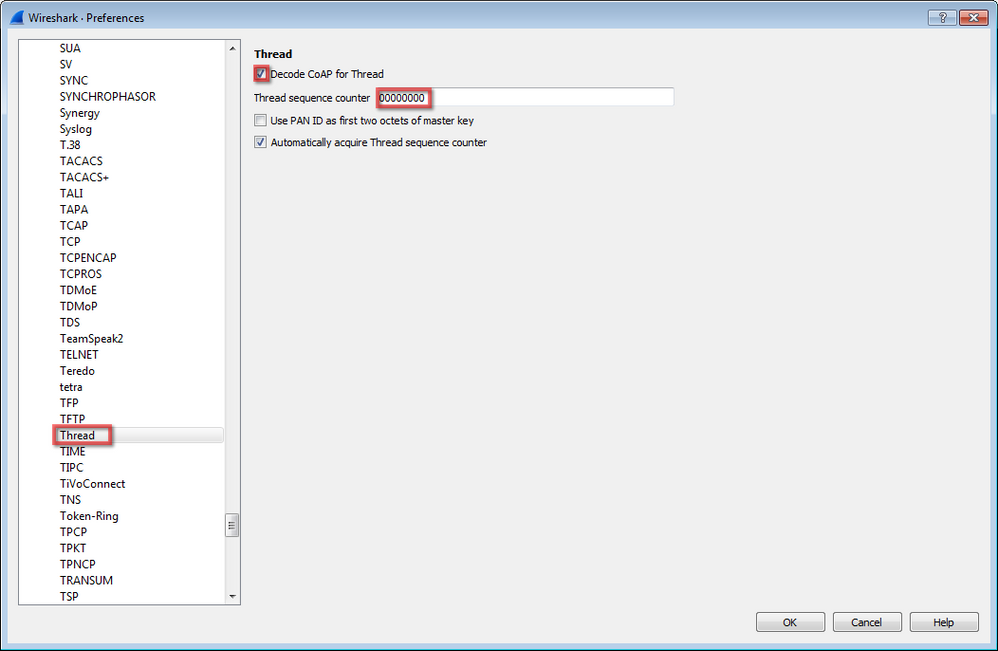
- Click Thread and select Decode CoAP for Thread with Thread sequence counter = 00000000 as shown below
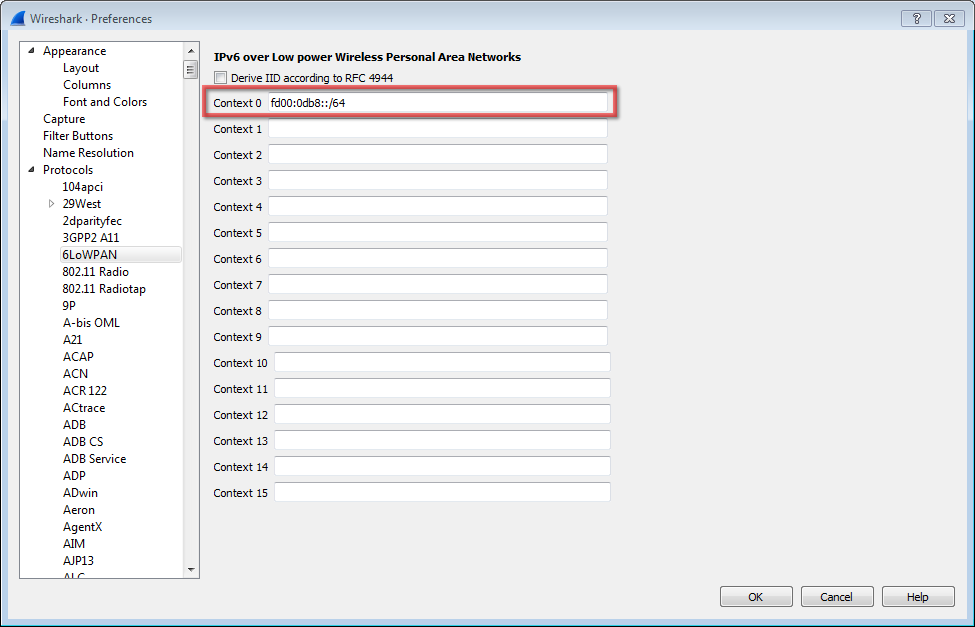
- At the 6LoWPAN preferences, add the Context 0 value of fd00:0db8::/64
- Click OK and close Wireshark
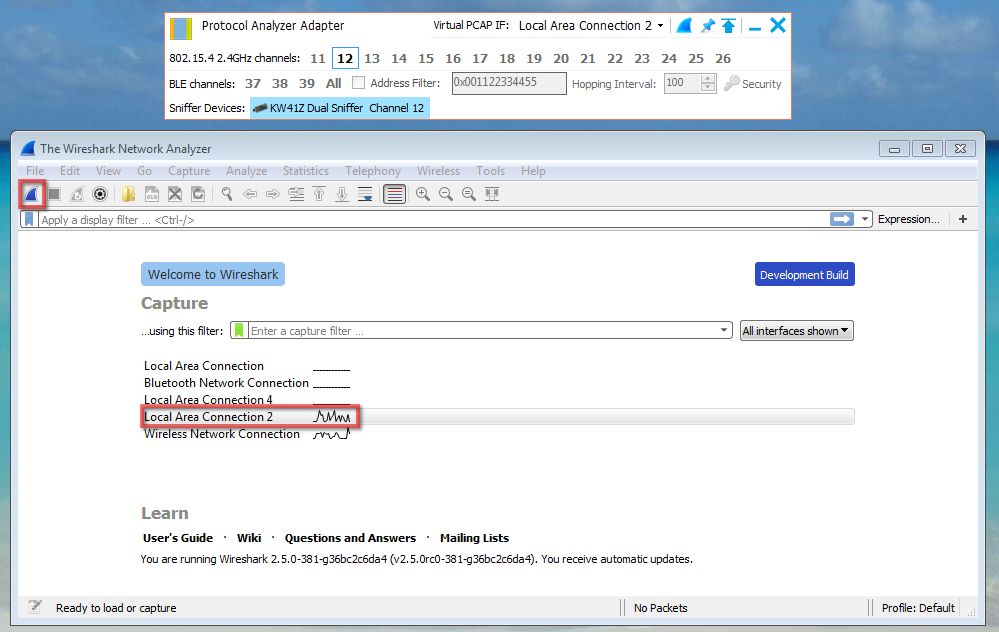
Configure Kinetis Protocol Analyzer
- Connect the USB-KW41Z to one of the USB ports on your computer
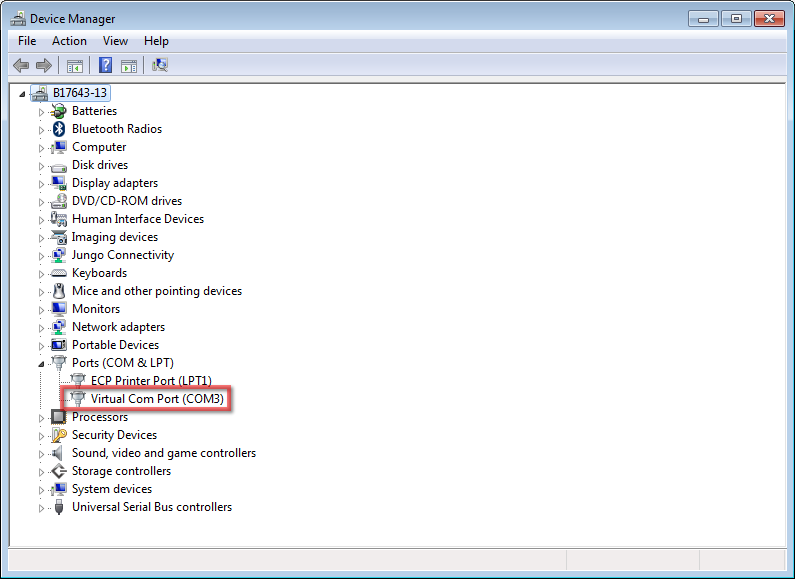
- Open the device manager and look for the device connected port
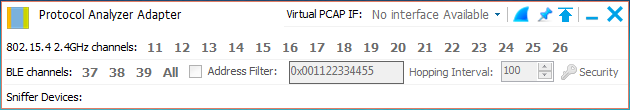
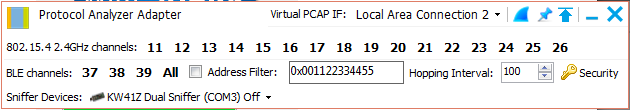
- Open the "Kinetis Protocol Analyzer Adapter" program
- Make sure, you have a USB-KW41Z connected to your PC when opening the program because the Kinetis Protocol Adapter will start looking for kinetis sniffer hardware. Once the USB-KW41Z is detected, the previously identify COM port will be displayed
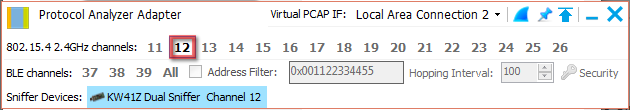
- Select the desired IEEE 802.15.4 channel to scan in the Kinetis Protocol Analyzer window. This guide selects channel 12 as an example
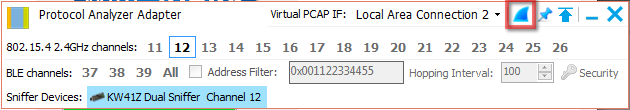
- Click on the Wireshark icon to open Wireshark Network Protocol Analyzer
An error may appear while opening Wireshark, click OK and continue
Wireshark Sniffing
- Wireshark Network Analyzer will be opened. On the "Capture" option of the main window, select the Local Area Connection that was created by the Kinetis Protocol Analyzer, in this example, Kinetis Protocol Analyzer created "Local Area Connection 2", then click "Start" button.
- USB-KW41Z will start to sniff and upcoming data will be displayed in the "Capture" window of the Wireshark Network Protocol Analyzer.
No ratings