- Forums
- Product Forums
- General Purpose MicrocontrollersGeneral Purpose Microcontrollers
- i.MX Forumsi.MX Forums
- QorIQ Processing PlatformsQorIQ Processing Platforms
- Identification and SecurityIdentification and Security
- Power ManagementPower Management
- Wireless ConnectivityWireless Connectivity
- RFID / NFCRFID / NFC
- Advanced AnalogAdvanced Analog
- Neural Processing UnitsNeural Processing Units
- MCX Microcontrollers
- S32G
- S32K
- S32V
- MPC5xxx
- Other NXP Products
- S12 / MagniV Microcontrollers
- Powertrain and Electrification Analog Drivers
- Sensors
- Vybrid Processors
- Digital Signal Controllers
- 8-bit Microcontrollers
- ColdFire/68K Microcontrollers and Processors
- PowerQUICC Processors
- OSBDM and TBDML
- S32M
- S32Z/E
-
- Solution Forums
- Software Forums
- MCUXpresso Software and ToolsMCUXpresso Software and Tools
- CodeWarriorCodeWarrior
- MQX Software SolutionsMQX Software Solutions
- Model-Based Design Toolbox (MBDT)Model-Based Design Toolbox (MBDT)
- FreeMASTER
- eIQ Machine Learning Software
- Embedded Software and Tools Clinic
- S32 SDK
- S32 Design Studio
- GUI Guider
- Zephyr Project
- Voice Technology
- Application Software Packs
- Secure Provisioning SDK (SPSDK)
- Processor Expert Software
- Generative AI & LLMs
-
- Topics
- Mobile Robotics - Drones and RoversMobile Robotics - Drones and Rovers
- NXP Training ContentNXP Training Content
- University ProgramsUniversity Programs
- Rapid IoT
- NXP Designs
- SafeAssure-Community
- OSS Security & Maintenance
- Using Our Community
-
- Cloud Lab Forums
-
- Knowledge Bases
- ARM Microcontrollers
- i.MX Processors
- Identification and Security
- Model-Based Design Toolbox (MBDT)
- QorIQ Processing Platforms
- S32 Automotive Processing Platform
- Wireless Connectivity
- CodeWarrior
- MCUXpresso Suite of Software and Tools
- MQX Software Solutions
- RFID / NFC
- Advanced Analog
- Neural Processing Units
-
- NXP Tech Blogs
- Home
- :
- MCUXpresso Software and Tools
- :
- MCU Bootloader
- :
- Re: Cant Write FSEC, SEC bits using FCA
Cant Write FSEC, SEC bits using FCA
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
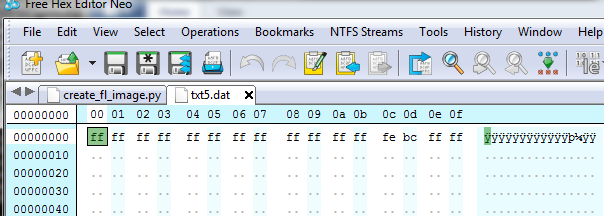
I am trying to secure my internal flash on Kineris K81 MCU, using the Flash Configuration Area,
All the Bits I configuring as follows
__FlashConfig
DCD 0x9BABEAF8 ; [0x400 - 0x403] Backdoor Key Access
DCD 0x9BABEAF8 ; [0x404 - 0x407] Backdoor Key Access
DCD 0xFFFFFFFF ; [0x408 - 0x40B] Program Flash Protection Register
DCD 0xFFFFBCFF ; [0x40C - 0x40F] 0x40C: FSEC, 0x40D FOPT, 0x40E-F Reserved,
__FlashConfig_End
where 0x40C is the SEC field configured as 11, which means that the flash is secured.
But the problem is that when I try to read this configuration using the blhost utility I find the Flash Security in UNSECURED state, and the command
blhost.exe -p COM3 read-memory 0x400 16 ./FCA.dat yields the following
Can any one tell why the SEC setting are beings always set as 'E' 1110 where 10 is unsecure?
Solved! Go to Solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Saurabh,
If you just want to use the blhost to check the 0X40C data, and you find the 0X40C still 0XFE and not the 0XFF which you want to download.
I don't know how you download the secured code to the chip? Some IDE or the debugger need to do the configuration, otherwise the secure area won't be updated.
I highly suggest you generate the .hex file, then check the 0X40C at first, make sure the app.hex 0X40C is really 0XFF, then you can use the blhost download that app, then check it again.
As I know, the IAR need to do the specific configuation, the KDS or MCUXpresso associate with the P&E debugger also may have problem, so, if you still want to use the debugger to download the code, I suggest you use the JLINK, when you select the chip, you must select the chip with partnumber<allow security>, then you can use the JLINK commander window, with JLINK commander: loadfile app.hex addr to download the code.
Please try it again in you side.
If you still have question about it, please kindly let me know.
Have a great day,
Kerry
-----------------------------------------------------------------------------------------------------------------------
Note: If this post answers your question, please click the Correct Answer button. Thank you!
-----------------------------------------------------------------------------------------------------------------------
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Saurabh,
If you just want to use the blhost to check the 0X40C data, and you find the 0X40C still 0XFE and not the 0XFF which you want to download.
I don't know how you download the secured code to the chip? Some IDE or the debugger need to do the configuration, otherwise the secure area won't be updated.
I highly suggest you generate the .hex file, then check the 0X40C at first, make sure the app.hex 0X40C is really 0XFF, then you can use the blhost download that app, then check it again.
As I know, the IAR need to do the specific configuation, the KDS or MCUXpresso associate with the P&E debugger also may have problem, so, if you still want to use the debugger to download the code, I suggest you use the JLINK, when you select the chip, you must select the chip with partnumber<allow security>, then you can use the JLINK commander window, with JLINK commander: loadfile app.hex addr to download the code.
Please try it again in you side.
If you still have question about it, please kindly let me know.
Have a great day,
Kerry
-----------------------------------------------------------------------------------------------------------------------
Note: If this post answers your question, please click the Correct Answer button. Thank you!
-----------------------------------------------------------------------------------------------------------------------
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
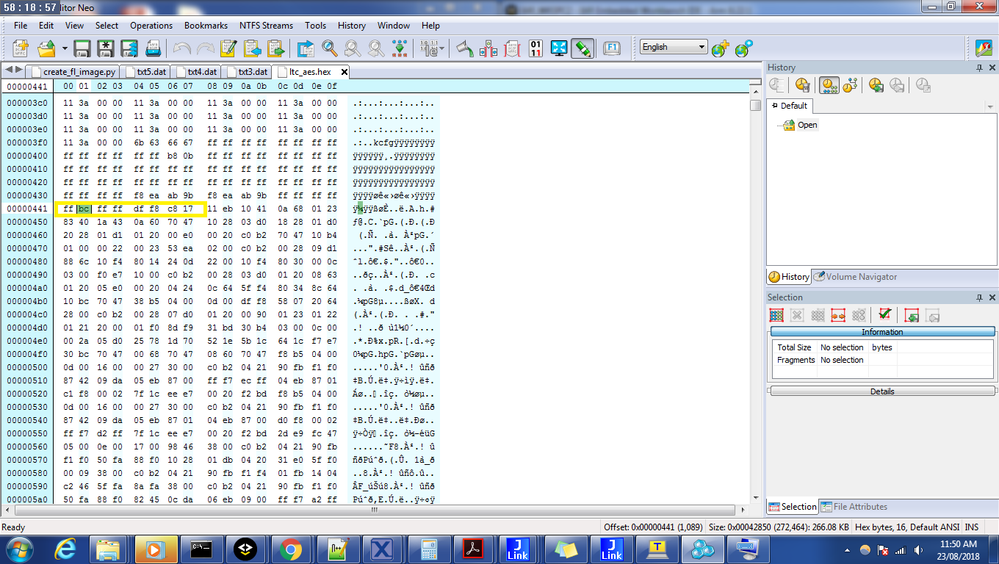
Hi Kerry,
I am using IAR, the final HEX shows the FSEC's SEC bit to be (11), But when I flash that I get (10),
Below is the snapshot, I using Jlink Commander to flash the MCU after doing a Erase chip.
I cant understand why its being forced into a unsecure state.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
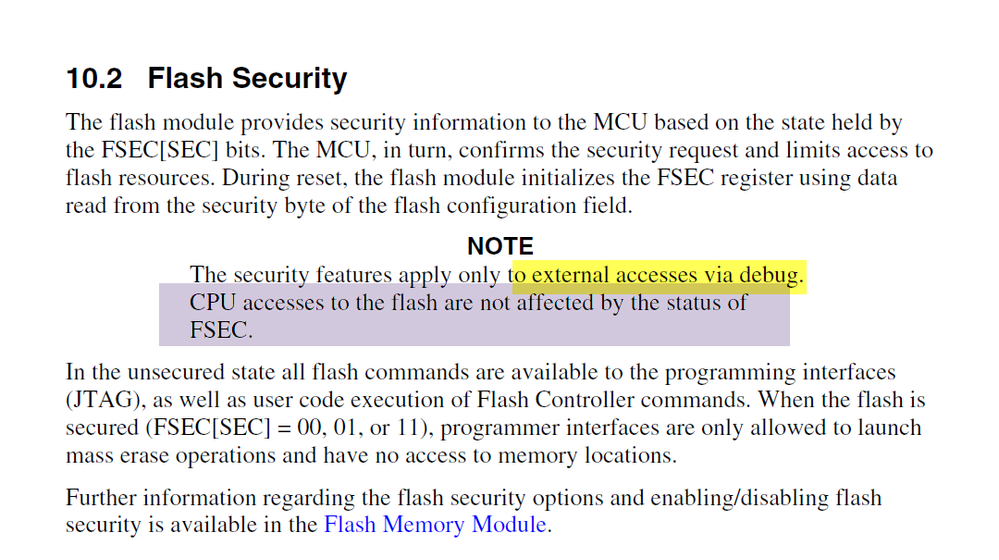
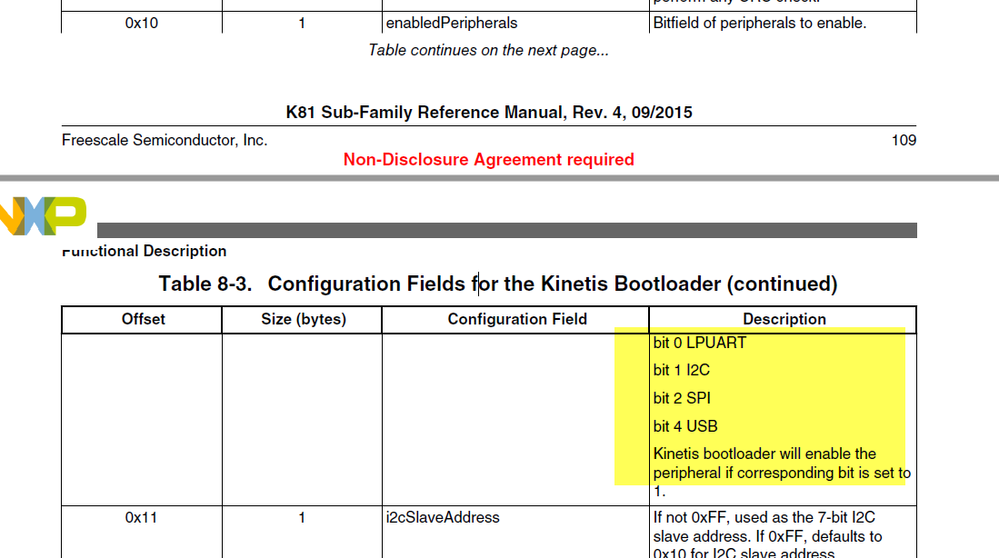
Hi Saurabh,
You are misunderstanding the FSEC secure function.
Please check the K81 reference manual:
FSEC is just limit the debug access through the SWD/JTAG interface, it won't limit the ROM bootloader function.
If you also don't want the ROM bootloader function work, you can can configure the BCA area, just disable the according ROM bootloader interface:
Wish it helps you!
Have a great day,
Kerry
-----------------------------------------------------------------------------------------------------------------------
Note: If this post answers your question, please click the Correct Answer button. Thank you!
-----------------------------------------------------------------------------------------------------------------------