- Forums
- Product Forums
- General Purpose MicrocontrollersGeneral Purpose Microcontrollers
- i.MX Forumsi.MX Forums
- QorIQ Processing PlatformsQorIQ Processing Platforms
- Identification and SecurityIdentification and Security
- Power ManagementPower Management
- Wireless ConnectivityWireless Connectivity
- RFID / NFCRFID / NFC
- Advanced AnalogAdvanced Analog
- Neural Processing UnitsNeural Processing Units
- MCX Microcontrollers
- S32G
- S32K
- S32V
- MPC5xxx
- Other NXP Products
- S12 / MagniV Microcontrollers
- Powertrain and Electrification Analog Drivers
- Sensors
- Vybrid Processors
- Digital Signal Controllers
- 8-bit Microcontrollers
- ColdFire/68K Microcontrollers and Processors
- PowerQUICC Processors
- OSBDM and TBDML
- S32M
- S32Z/E
-
- Solution Forums
- Software Forums
- MCUXpresso Software and ToolsMCUXpresso Software and Tools
- CodeWarriorCodeWarrior
- MQX Software SolutionsMQX Software Solutions
- Model-Based Design Toolbox (MBDT)Model-Based Design Toolbox (MBDT)
- FreeMASTER
- eIQ Machine Learning Software
- Embedded Software and Tools Clinic
- S32 SDK
- S32 Design Studio
- GUI Guider
- Zephyr Project
- Voice Technology
- Application Software Packs
- Secure Provisioning SDK (SPSDK)
- Processor Expert Software
- Generative AI & LLMs
-
- Topics
- Mobile Robotics - Drones and RoversMobile Robotics - Drones and Rovers
- NXP Training ContentNXP Training Content
- University ProgramsUniversity Programs
- Rapid IoT
- NXP Designs
- SafeAssure-Community
- OSS Security & Maintenance
- Using Our Community
-
- Cloud Lab Forums
-
- Knowledge Bases
- ARM Microcontrollers
- i.MX Processors
- Identification and Security
- Model-Based Design Toolbox (MBDT)
- QorIQ Processing Platforms
- S32 Automotive Processing Platform
- Wireless Connectivity
- CodeWarrior
- MCUXpresso Suite of Software and Tools
- MQX Software Solutions
- RFID / NFC
- Advanced Analog
- Neural Processing Units
-
- NXP Tech Blogs
- Home
- :
- 通用微控制器
- :
- Kinetis微控制器
- :
- LTC AES-256 CBC across multiple blocks
LTC AES-256 CBC across multiple blocks
Hi All
I can do AES-256 encryption and decryption with mmCAU, mbedTLS, OpenSSL and WolfSSL but am having problems with decryption with LTC.
My test consists of receiving a stream of encrypted data (AES-256 key known and also the IV initial state known and synchronised). The decryption takes place in 1k blocks.
1. The first test showed that the first 1k block was correctly decrypted but subsequent ones were not.
2. I then investigated and tested different methods of setting the decrypt key, which led me to identify a strange behavior as reported here: https://community.nxp.com/thread/488540
3. Related to the way that the decrypt key is set I found that if I set the key differently (so that the error interrupt doesn't get set - see other post) the first 1k block decryption fails BUT the second block decryption is then successful. Subsequent blocks again fail.
4. In both cases I watch the IV register values before and after decrypting the first block and they are the same in each case and match the values that mmCAU or SW implementations have.
Can anyone explain how the way that the decrypt key is set can have such an effect on decryption operation?
What is causing the subsequent block decryption to fail when IV values look to be correct?
Any tricks to get it working over multiple blocks in a stream?
Regards
Mark
已解决! 转到解答。
Hi Al
I managed to solve it but the KDS examples don't (or can't) do it - they only do single block decrypts.
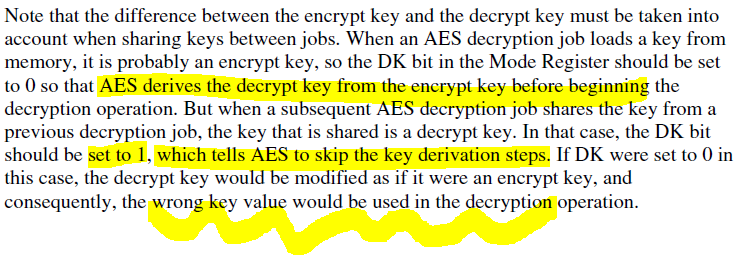
The trick is to not reset the keys/IV after a block decrypt (which the examples always do) and use the mode register's AES decrypt key bit (DK) on subsequent blocks since the first block decrypt automatically convert the loaded encrypt key to a decrypt key and if the DK bit is left cleared for subsequent blocks it does it again, which corrupts it.
It is explained in the user's manual but takes a bit of time before it becomes clear and finally making any sense:
Regards
Mark
Hi Al
I managed to solve it but the KDS examples don't (or can't) do it - they only do single block decrypts.
The trick is to not reset the keys/IV after a block decrypt (which the examples always do) and use the mode register's AES decrypt key bit (DK) on subsequent blocks since the first block decrypt automatically convert the loaded encrypt key to a decrypt key and if the DK bit is left cleared for subsequent blocks it does it again, which corrupts it.
It is explained in the user's manual but takes a bit of time before it becomes clear and finally making any sense:
Regards
Mark