- Forums
- Product Forums
- General Purpose MicrocontrollersGeneral Purpose Microcontrollers
- i.MX Forumsi.MX Forums
- QorIQ Processing PlatformsQorIQ Processing Platforms
- Identification and SecurityIdentification and Security
- Power ManagementPower Management
- Wireless ConnectivityWireless Connectivity
- RFID / NFCRFID / NFC
- Advanced AnalogAdvanced Analog
- Neural Processing UnitsNeural Processing Units
- MCX Microcontrollers
- S32G
- S32K
- S32V
- MPC5xxx
- Other NXP Products
- S12 / MagniV Microcontrollers
- Powertrain and Electrification Analog Drivers
- Sensors
- Vybrid Processors
- Digital Signal Controllers
- 8-bit Microcontrollers
- ColdFire/68K Microcontrollers and Processors
- PowerQUICC Processors
- OSBDM and TBDML
- S32M
- S32Z/E
-
- Solution Forums
- Software Forums
- MCUXpresso Software and ToolsMCUXpresso Software and Tools
- CodeWarriorCodeWarrior
- MQX Software SolutionsMQX Software Solutions
- Model-Based Design Toolbox (MBDT)Model-Based Design Toolbox (MBDT)
- FreeMASTER
- eIQ Machine Learning Software
- Embedded Software and Tools Clinic
- S32 SDK
- S32 Design Studio
- GUI Guider
- Zephyr Project
- Voice Technology
- Application Software Packs
- Secure Provisioning SDK (SPSDK)
- Processor Expert Software
- Generative AI & LLMs
-
- Topics
- Mobile Robotics - Drones and RoversMobile Robotics - Drones and Rovers
- NXP Training ContentNXP Training Content
- University ProgramsUniversity Programs
- Rapid IoT
- NXP Designs
- SafeAssure-Community
- OSS Security & Maintenance
- Using Our Community
-
- Cloud Lab Forums
-
- Knowledge Bases
- ARM Microcontrollers
- i.MX Processors
- Identification and Security
- Model-Based Design Toolbox (MBDT)
- QorIQ Processing Platforms
- S32 Automotive Processing Platform
- Wireless Connectivity
- CodeWarrior
- MCUXpresso Suite of Software and Tools
- MQX Software Solutions
- RFID / NFC
- Advanced Analog
- Neural Processing Units
-
- NXP Tech Blogs
- Home
- :
- Topics
- :
- NXP Designs Knowledge Base
- :
- NFC for consumables and accessories
NFC for consumables and accessories
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
NFC for consumables and accessories
NFC for consumables and accessories
This post entry provides a detailed description of how NFC can be used for authentication and identification of consumables and accessories. This document has been structured as follows:
- NFC for product authentication and identification
- How NFC works in product authentication and identification
- Success stories
- How to implement the use case
- NFC portfolio for authentication and identification applications
- NXP originality signature
- OEM customizable orignality signature
- Secure unique NFC message (SUN)
- AES three-pass mutual authentication
- NFC tag security feature comparison
- NFC frontends comparison
- NFC Nutshell kit
- NFC Nutshell kit components
- Modes of operation for the USB protocol converter module
- NXP development tools supported
- Consumable authentication using the NFC Nutshell kit
- Hardware preparation
- USB converter module configuration
- Software development with the NFC Reader Library
- NXP Originality signature verification
- Three-pass mutual authentication
- Build project with MCUXpresso
- Create .hex file with MCUXpresso
- Flash the MCU image with Flash Magic tool
- Debugging mode
- Video recorded session
- Available resources
NFC for product authentication and identification
NFC is a useful addition to verify product authenticity and identification. There are plenty of examples where NFC fits nicely, for instance:
- For anti-counterfeit protection and safe brand reputation.
- For identifying users and provide personalized interactions
- For sending notifications when accessories need to be replaced
- And to automatically adjust settings of the main unit based on the accessory attached.
These are just a few examples so you grasp the potential of NFC in such scenarios.
How NFC works in product authentication and identification
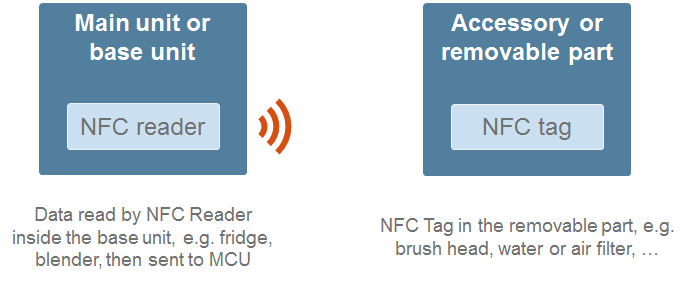
Into the scope of a consumable or accessories authentication via NFC, there are always two components involved.
- On the one hand, there is one main unit. This is the device where you can plug the part or the accessory. Typically, this main unit would include an active NFC reader.
- On the other hand, the consumable or replacement would include and NFC tag.
The NFC reader in the main unit can detect when the removable part is connected. As soon as the replacement is connected, it reads the information stored in the tag and uses it to verify the accessory originality. Precisely, the information and security features implemented in the tag is what allows the main unit to:
- First, authenticate that is a genuine accessory
- And optionally, configure related settings depending on the accessory.
Success stories
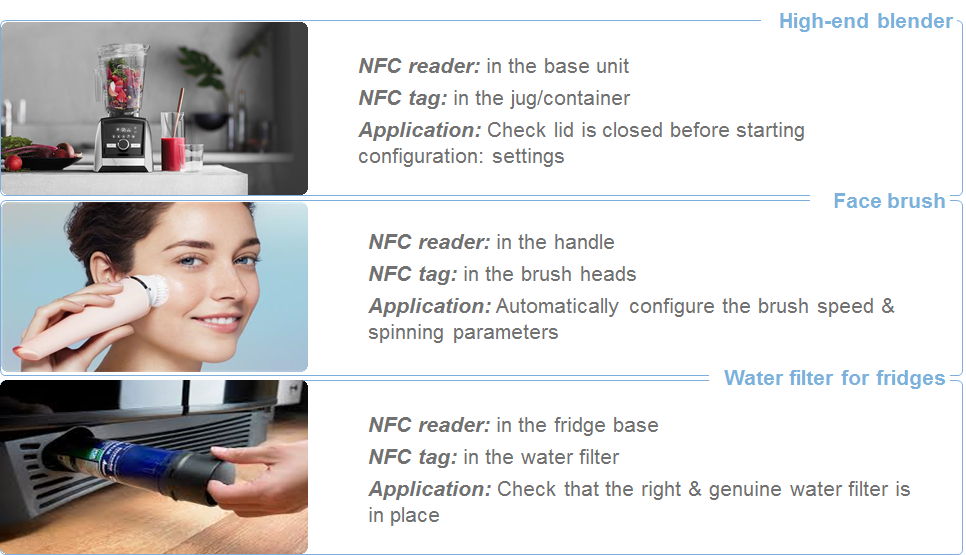
The NFC authentication is not a proof-of-concept but rather a consolidated solution. There are already some success stories in the market. For example:
- A high-end blender that uses NFC to verifies the authenticity of the containers and cups used. In addition, the blender adjusts the speed parameters automatically per each different container. As mentioned, the NFC reader is part of the base unit while the tag is part of each container.
- Another example, a face brush that make sure that the brush head is genuine. As before, the reader in on the base while the tag is on each head brush. When a new head brush is connected it check its validity and adjust the settings.
- The third example is a fridge that discards non-original water filters and check if the fridge and filter models are compatible.
How to implement the use case
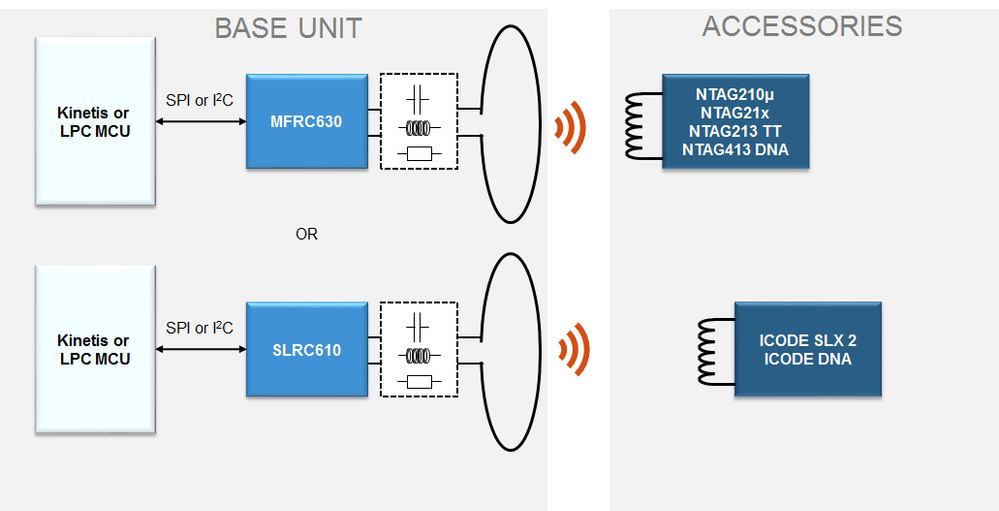
From a simplified block diagram perspective, the base unit embed an NFC reader, this NFC reader is made of an NFC frontend, generating the RF field and a Host MCU, loaded with the application firmware. On the other hand, the accessory, beds an NFC tag. The MFRC630 or our SLRC610 are recommended options from the reader side, while the NTAG and ICODE families are recommended from the tag side. The final product selection depends on your specific application requirements
There are a few questions that you can ask yourself to know which product fits you best.
- First, what is your application about? Are you looking for brand protection? Or counterfeit detection? Or settings customization?
- Second, what kind of security you need? You need device identification, or you also would like encrypted data exchange?
- Third, what reading distance is required in your system? Are we talking about a centimeters or tenths of centimiters?
- And, in relation implementation details, are there any specific size constrains? Is there metal in the surrounding? Etc.
NFC portfolio for authentication and identification applications
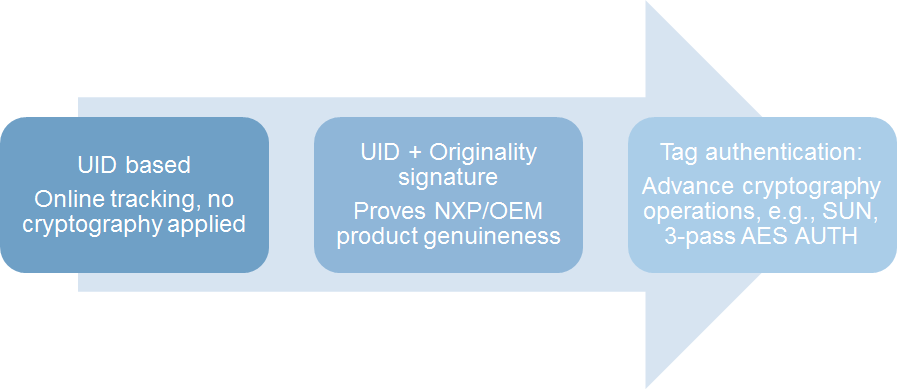
I organized the security features for consumable authentication in three groups:
- There is a basic level security level where the tag UID is used for proof-of-origin. In this case, there is no crypto protocols applied and the verification consists on checking whether the UID is in our database or not.
- There is a second level, where the authentication is proven using an originality signature. Depending on the solution, this can be an NXP- signature or a customer-specific signature.
- There is a third level, that uses a cryptographic three pass mutual authentication as a verification mechanism.
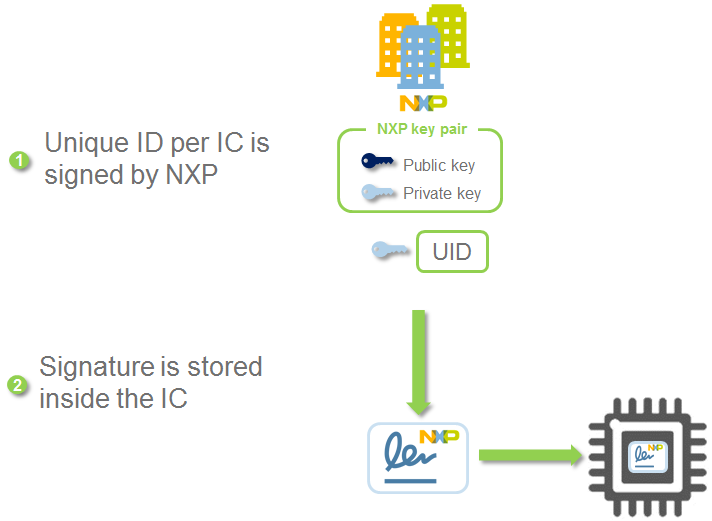
NXP originality signature
The originality signature implemented in NTAG and ICODE families is based on standard Elliptic Curve Cryptography. NXP generates a ECC key pair (a public and a private key) that are stored in a secure server. In asymmetric crypto, a signature is generated by a signing algorithm given a message and a private key. During production, NXP takes care of provisioning a die-individual signature in each IC. This signature is generated using the tag’s UID and the NXP private key. Since each tag has a different UID, a unique signature is stored in each tag. Therefore, the tags leave the NXP factory already with this unique signature pre-programmed in the IC memory.
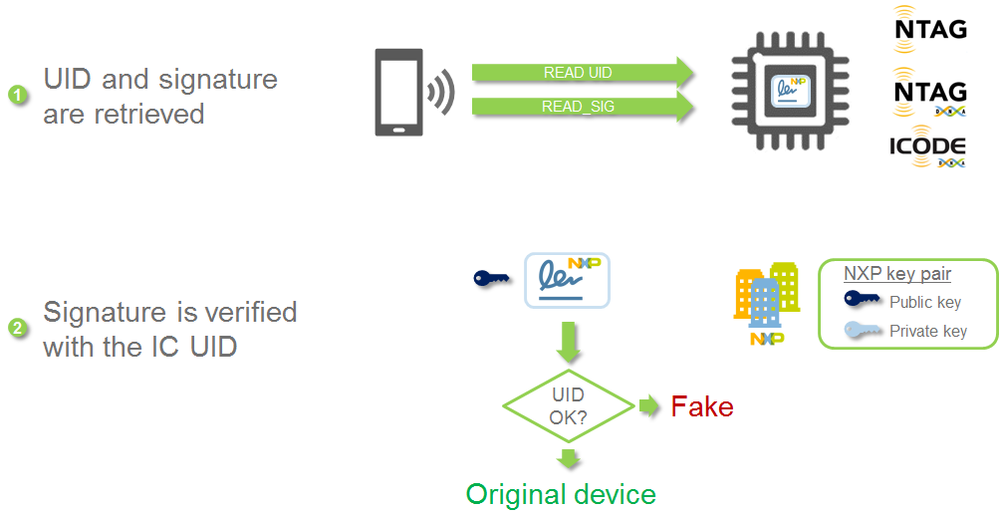
These pre-provisioned tags are integrated by OEM into their final devices & accessories. On the field, the originality signature verification process is as follows:
- First, the reader unit reads the tag UID.
- Second, the reader retrieves the tag signature with the READ_SIGNATURE command.
- Third, the reader can verify this tag originality signature using the corresponding ECC public key and the tag’s UID.
With this feature, it is possible to verify with confidence that the tag is using an IC manufactured by NXP and not a cloned IC. In case that the public key is stored in the reader, the entire process can be performed offline. The products supporting this functionality are: NTAG21x, NTAG413 DNA, NTAG I2C plus, NTAG21x F and ICODE SLIX2.
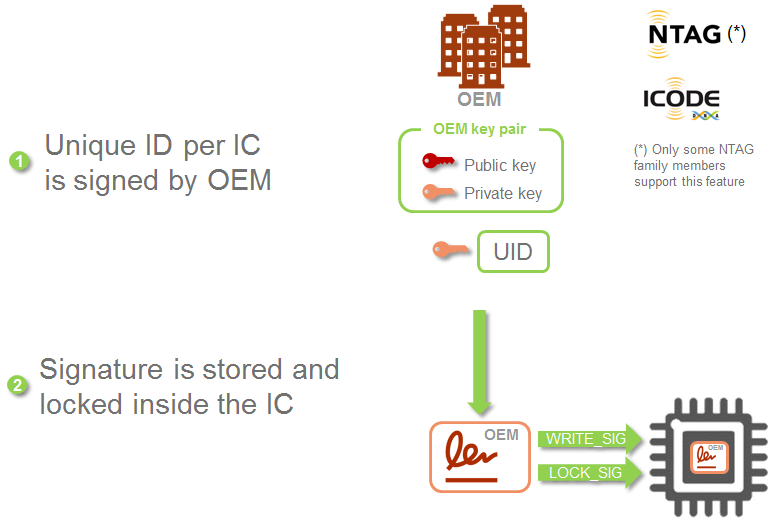
OEM customizable orignality signature
The NFC tags come pre-programmed with an NXP originality signature. However, some NTAG and ICODE family members also offer the possibility to customize the originality signature per OEM. The process is similar to the one described above, but in this case, the OEM provisions each tag with a die-individual signature, and lock it to avoid unauthorized overwriting.
On the field, the tag originality signature verification is done in the same way:
- The reader retrieves the tag UID and tag signature
- The reader uses the corresponding OEM public key and tag UID to verify the signature.
The main benefit of customizing the originality signature is that, in addition, it allows to verify that the product belongs to the OEM and not from another manufacturer. The products supporting customer originality signature are NTAG210u, NTAG 213 TT and ICODE DNA.
Secure unique NFC message (SUN)
One security level up, we find solutions like our NTAG 413 DNA which enable a new Secure Unique NFC message (SUN) feature. This SUN feature generates a unique, secure authentication code each time the tag is tapped. This tap-unique data consists of an NDEF formatted packet that includes:
- A URL
- The tag UID
- The tap counter
- And a AES-based CMAC calculated over the UID, the counter and the URL.
This CMAC is dynamic and changes over each tap since the counter is increased every time. The cloud service verifies the authenticity of the message with the appropriate symmetric keys. With this tag, any NFC enabled device (including Android and the recent iOS 11 devices) can automatically connect to a web based service and based on the information contained in URL, the device can check the tags authenticity and verify the information validity.
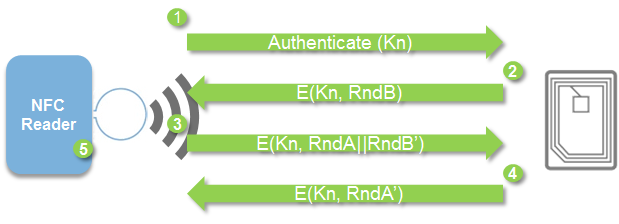
AES three-pass mutual authentication
The last tag security feature is the AES mutual authentication, which is supported by our NTAG 413 DNA as well as the ICODE DNA. The mutual authentication:
- It is based on a shared secret key known by both endpoints
- It allows us to verify both ends of the communication (not just the accessory).
.
The AES 3 pass mutual authentication consist of probing to the other end the knowledge of a secret, in this case, the knowledge of a secret AES key. As we do not want to share in plain this secret over an unsecure channel, the mechanism is based on the encryption of random challenges using this secret key. If both ends are capable of verifying this random-challenge scheme, they demonstrate that the other end knows the secret, and therefore, they prove their authenticity.
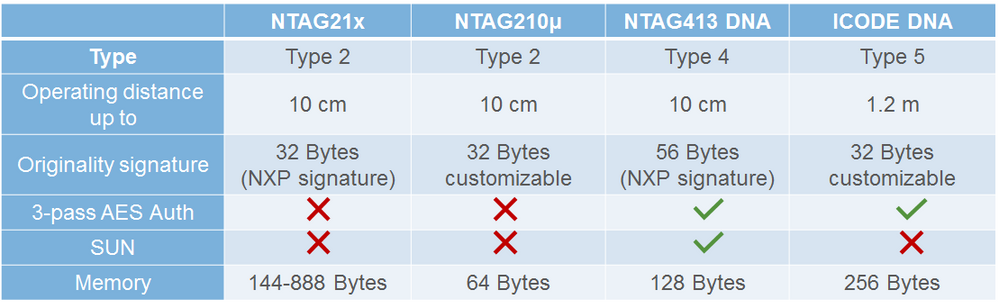
NFC tag security feature comparison
The following table consolidates the different NFC tag security options:
- The NTAG21x support NXP originality signature
- The NTAG210u is a cost optimized version with customizable originality signature
- The NTAG413 DNA offers the SUN feature as well as AES authentication and encryption
- Finally, the ICODE DNA comes with customizable originality signature and AES authentication.
Therefore, the NTAG413 DNA and ICODE DNA are the strongest authentication options that we have right now in the tag portfolio. The reading distance will influence on the decision between NTAG or ICODE:
- NTAG is an ISO14443 compliant tag with a operating distance of a few centimiters.
- ICODE is an ISO15693 compliant tag with an operating distance of tens of centimers.
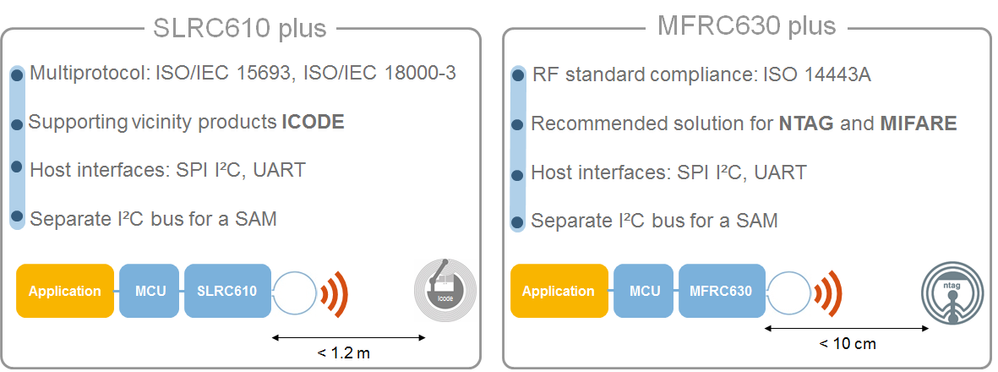
NFC frontends comparison
Regarding the NFC readers for the base unit side, we most ideal solutions are:
- The SLRC610 plus if your application needs a reading distance of tens of centimiters. The SLRC610 supports ISO15693 and is fully operational with our ICODE family.
- The MFRC630 if your applications needs a reading distance of a few centimiters. The MFRC630 supports ISO14443-A and is fully operational with our NTAG family.
NFC Nutshell kit
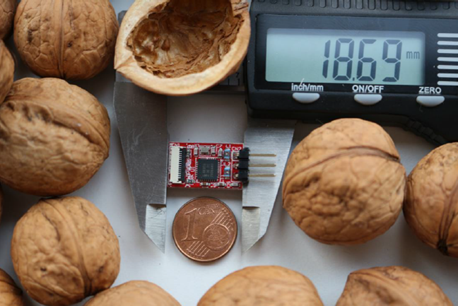
This section leverages on the NFC Nutshell kit to explain how to develop your own NFC authentication solution. This kit was developeb by GMMC an approved engineering consultant of NXP. The NFC Nutshell kit is a set of hardware modules that can be used for:
- NFC integration into new designs or retrofitting into existing products thanks to its small size.
- It can be used to build NFC demonstrators
- Or, it can be used for evaluation, development and testing of NFC applications
The main benefits offered by the NFC Nutshell kit are that:
- It is made to provide designers with Nano sized hardware modules which can be configured and combined in a variety of ways.
- It was developed with flexibility in mind so that designers can easily combined different MCUs with different NFC frontends and multiple development environment easily.
- And, it is constructed and prepared to be compatible with NXP software tools.
NFC Nutshell kit components
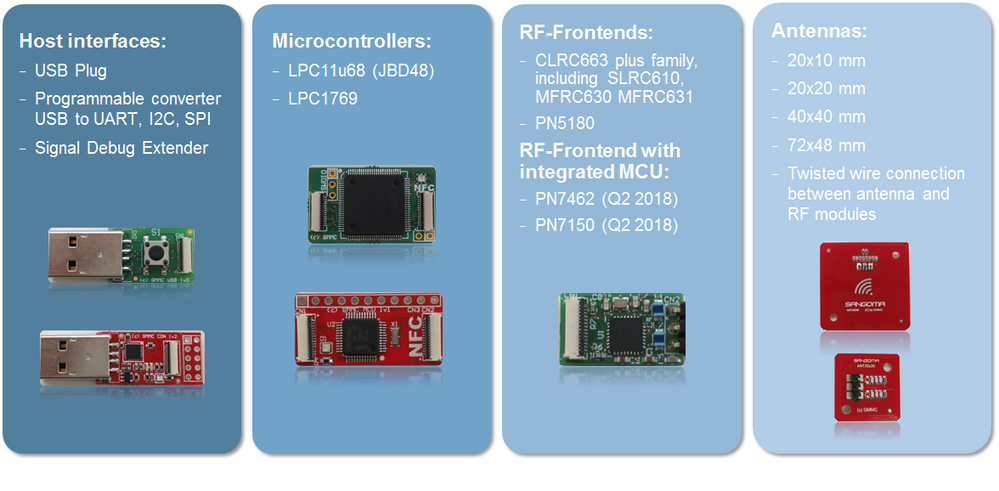
The kit includes a good bunch of modules that be divided in 4 different groups:
- Host interface modules
- A USB plug that bridges the USB communication to the Host MCU
- A USB converter that is used to communicate over UART, I2C or SPI with the host MCU
- A host interface signal debug extender
- MCU modules:
- LPC1769
- LPC11U68.
- NFC reader modules:
- CLRC663 plus
- PN5180
- And soon, PN7462 and PN7150
- Antenna PCBs of different sizes to test the performance over different antenna sizes (20x10mm, 20x20mm, 40x40mm, 72x48mm).
All the modules are connected with flexible flat cables, and the hardware components are designed for minimal PCB area to demonstrate integration into space constrained products.
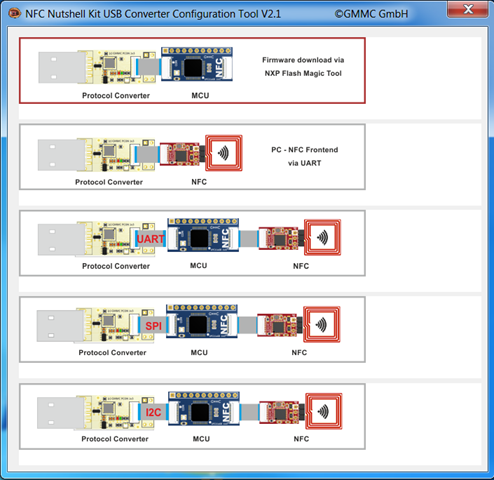
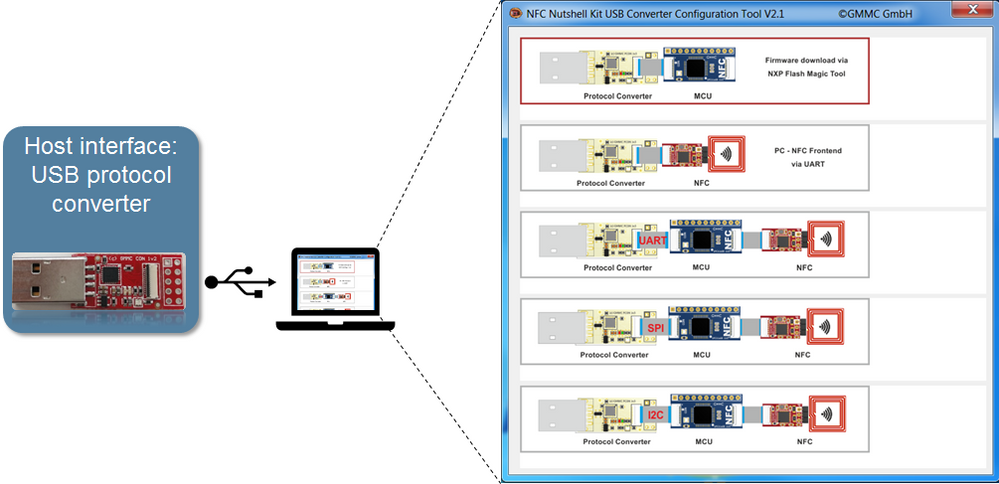
Modes of operation for the USB protocol converter module
In our case, out of the different host interface modules, we select the USB to I²C, UART and SPI converter. This single module itself has several configuration options. As part of the kit, a USB Protocol Converter Configure Tool is provided to easily configure the different operation modes of this component.
The user can open this tool and check the different options:
- The first one is used when the converter is connected to an MCU. It configures the module for an in-system-programming, which means we can use NXP Flash Magic Tool to program the MCU flash memory.
- The second option, the development PC communicates directly to the connected NFC frontend via UART.
- Last, we have 3 bridge modes for single protocol conversion. The Host system can send the any command over the USB interface and it will be converted to the chosen protocol, either I²C, SPI or UART.
NXP development tools supported
Another nice feature of this NFC Nutshell kit is its native support of NXP development tools. Using this kit, you can seamlessly run:
- The NFC Cockpit, an intuitive graphic user interface that lets you configure and adapt IC settings without writing a single line of software code.
- The RFIDDiscover PC tool, a user-friendly GUI for evaluation of NTAGs, ICODEs or MIFARE Cards. It is the software that is commonly used with NXP Pegoda reader.
- The NFC reader library, a complete SW support library for RF frontend ICs. The faster and more straightforward way to develop NFC applications.
Consumable authentication using the NFC Nutshell kit
This last section is meant to give insight on how to develop your own NFC authentication solution. For that, we will make use of the NFC Nutshell kit and existing software examples as a way to illustrate a possible development process. The five steps that we followed to run a tag signature verification software example in the NFC Nutshell kit are:
- First, we select and connect the right modules together
- Second, we configure the host system interface according to our SW development environment.
- After that, we develop the application logic of our use case.
- When the code is ready, we build the project, and create the binary file.
- And last, we use the Flash Magic tool to install the binary file.
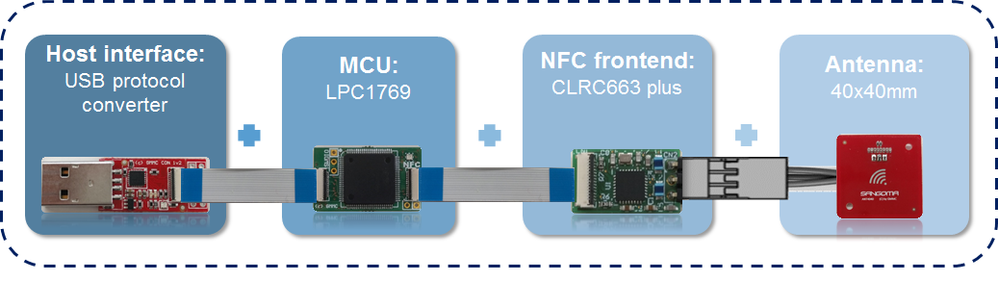
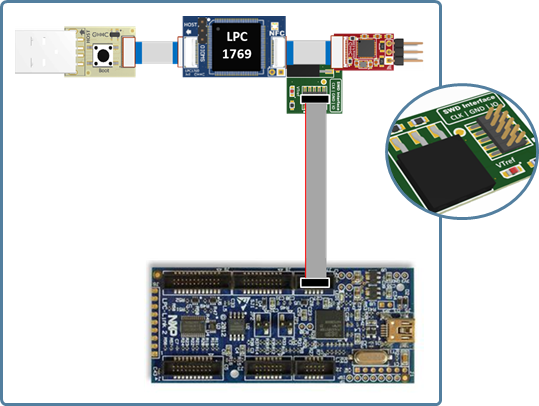
Hardware preparation
About the hardware preparation… the modules selected are:
- The USB protocol converter module, as an interface converter between the development PC and the reader host MCU.
- The LPC1769 as the reader host MCU
- The CLRC663 as NFC frontend
- And, the 40x400 mm PCB antenna.
USB converter module configuration
Before going to the software development itself, we need to configure the USB protocol converter. The USB protocol converter mode of operation configuration is a straight forward process. We just need to execute the Configure Tool provided in the kit, and select the mode compatible for Flash Magic. In this case, this setting corresponds to the first choice as shown in the screenshot.
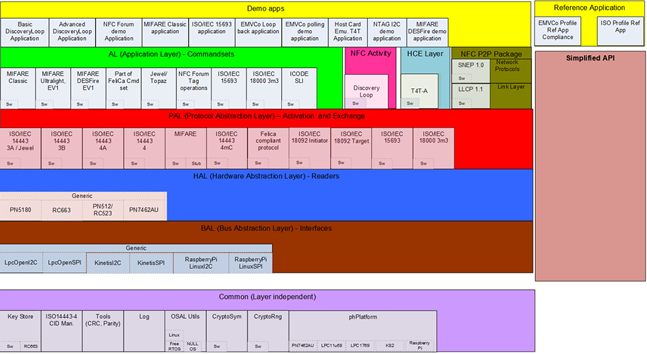
Software development with the NFC Reader Library
For the application software development, we leverage on our well know NFC Reader Library. The NFC Reader Libary is a complete API for developing NFC and MIFARE-based applications, it is free of charge and the latest release can be downloaded from www.nxp.com/pages/:NFC-READER-LIBRARY. Great news is that the NFC Reader Library has:
- Native support for the modules we selected out the NFC Nutshell kit (the CLRC663 plus and LPC1769)
- Supports the proximity and vicinity RF protocols.
- And also, the commandset of Type 2, Type 4 and Type 5 tags.
Therefore, we can focus on developing the application logic rather than spending time on implementing drivers or the RF protocols. For that, we do not even need to start from scratch, because we can take as reference any of the eleven software examples. Each of these examples do not make use of the entire library, but just use the NFC Reader library components required for the use case demonstrate, allowing to reduce the overall memory footprint.
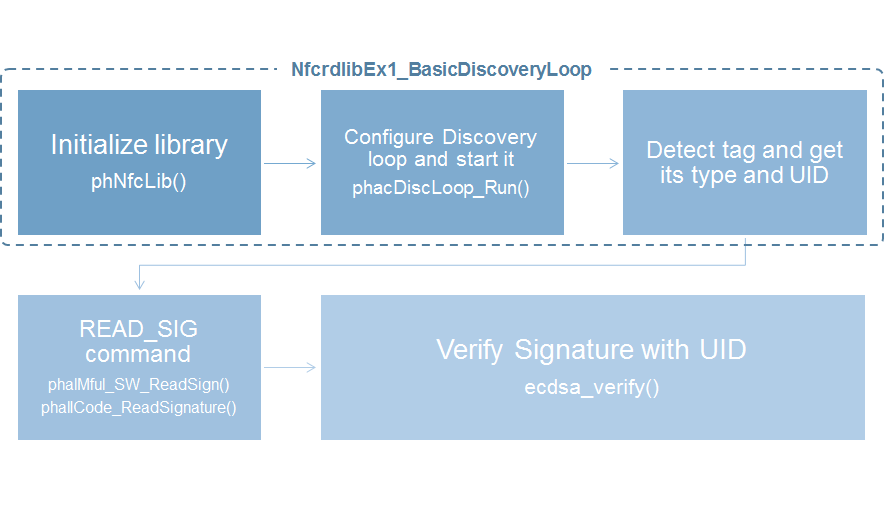
NXP Originality signature verification
We take the Basic Discovery loop example as a starting point for developing an piece of code for tag originality signature verification. If we have a look at the source code, this example:
- Initialize the library, this is initializing the SW components that will be used
- It configures the discovery loop for tag detection
- Keeps iterating until a tag is detected
Once the tag is detected, we mentioned that the signature verification process consisted of:
- Retrieving the UID
- Retrieving the signature
- Use a signing verification algorithm to check the signature
There are several libraries implementing ECC signature validation. As an example, we added an open source C library called nano-ECC into our project. The function call ecdsa_verify() can process the originality signature read from the tags. It is just as simple as passing as arguments, the UID the signature and the public key. In addition, the NTAG Originality signature validation application note provides code snipets and instructions for this process as well.
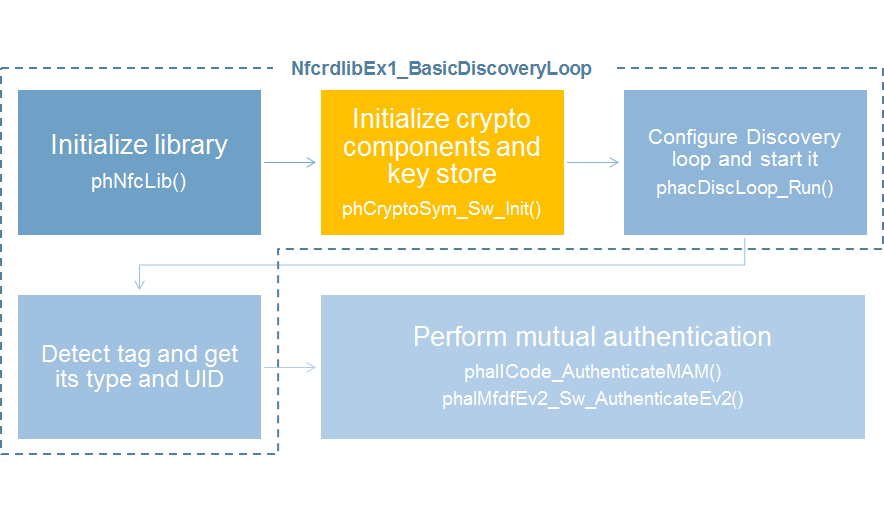
Three-pass mutual authentication
Another example for the implementation of a AES three-pass mutual authentication. Once again, we can take as a starting point the Basic Discovery loop example, which:
- Initializes the library, configures the discovery and iterates until a tag is detected.
- In addition, we need to add the crypto component in the NFC Reader Library handling the crypto calculation and key storage (in orange)
Once the tag is detected, we can make a direct API function call of the corresponding tag type, whether it is a Type 5 (ICODE) or a Type 4 tag (NTAG 413 DNA) there is the right function call in the lib for that. All the crypto complexity of the three pass mutual authentication is just hidden behing a single function call.
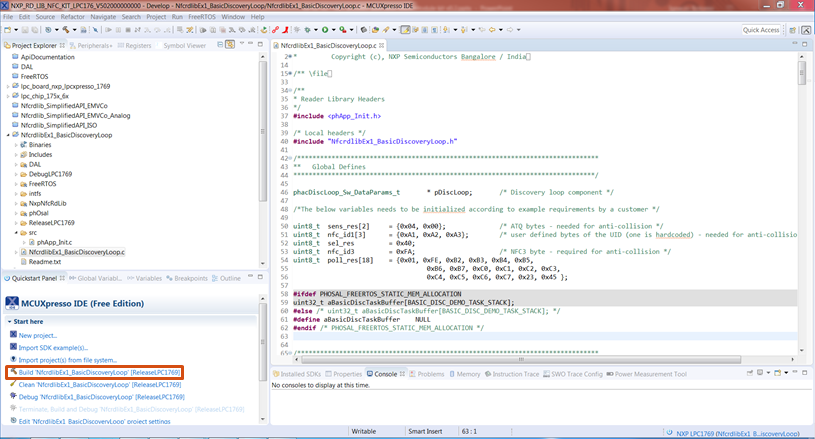
Build project with MCUXpresso
The MCUXpresso tools is used to build and compile the solution by clicking in the hammer button down in the quick start panel.
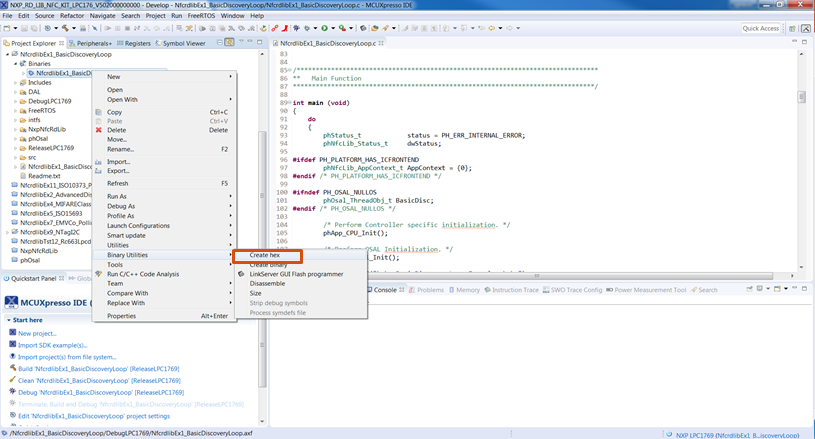
Create .hex file with MCUXpresso
After that, we can also generate the .hex file. For that, we just need to right click on the binary file, go to binary utilities and click on create hex file option.
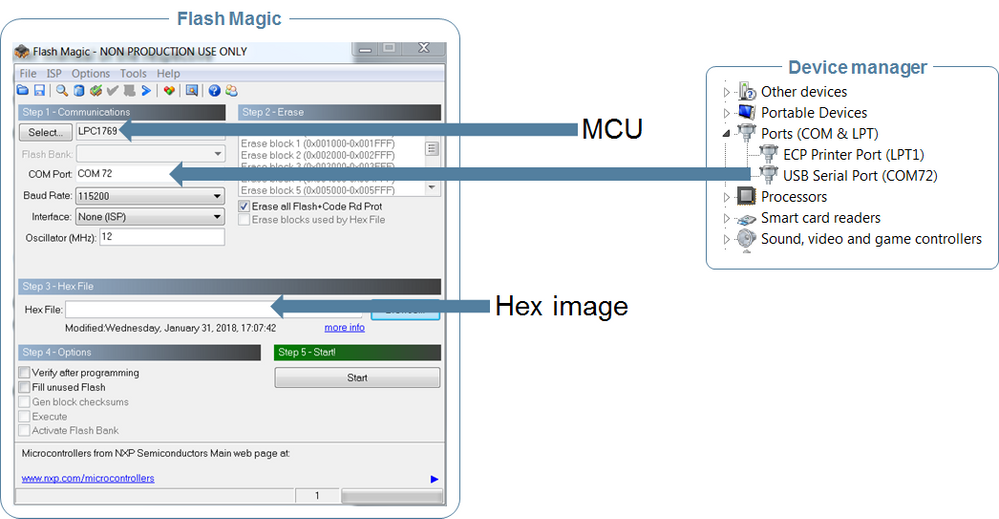
Flash the MCU image with Flash Magic tool
With the .hex file generated., the last step is to flash our MCU with this .hex file. In the Flash Magic tool menu, select:
- The MCU used, in this case LPc1769
- The COM port, which can be found in the Windows device manager, in our case COM72
- Select the path to the .hex file
- Click start
Once the flashing is completed, the USB converter setting should be changed to I2C or SPI configuration. At this moment, the solution is running and the application will try to authenticate any tag presented in front of the reader.
Debugging mode
Optionally, the NFC Nutshell kit also incorporates a code debugging mode. For that, there is an extra HW module compatible with LC1769 and LPC11U68 that can be used to interface with an LPC-Link2 debug probe.
Video recorded session
On 22 February 2018, a live session explaining the NFC for consumable and accessories solution was recorded. You can watch the recording here:
Available resources
The available resources referred to this post explanation are:
Tags:
Readers:
Application notes:
NFC Nutshell kit: