- Forums
- Product Forums
- General Purpose MicrocontrollersGeneral Purpose Microcontrollers
- i.MX Forumsi.MX Forums
- QorIQ Processing PlatformsQorIQ Processing Platforms
- Identification and SecurityIdentification and Security
- Power ManagementPower Management
- MCX Microcontrollers
- S32G
- S32K
- S32V
- MPC5xxx
- Other NXP Products
- Wireless Connectivity
- S12 / MagniV Microcontrollers
- Powertrain and Electrification Analog Drivers
- Sensors
- Vybrid Processors
- Digital Signal Controllers
- 8-bit Microcontrollers
- ColdFire/68K Microcontrollers and Processors
- PowerQUICC Processors
- OSBDM and TBDML
-
- Solution Forums
- Software Forums
- MCUXpresso Software and ToolsMCUXpresso Software and Tools
- CodeWarriorCodeWarrior
- MQX Software SolutionsMQX Software Solutions
- Model-Based Design Toolbox (MBDT)Model-Based Design Toolbox (MBDT)
- FreeMASTER
- eIQ Machine Learning Software
- Embedded Software and Tools Clinic
- S32 SDK
- S32 Design Studio
- GUI Guider
- Zephyr Project
- Voice Technology
- Application Software Packs
- Secure Provisioning SDK (SPSDK)
- Processor Expert Software
- MCUXpresso Training Hub
-
- Topics
- Mobile Robotics - Drones and RoversMobile Robotics - Drones and Rovers
- NXP Training ContentNXP Training Content
- University ProgramsUniversity Programs
- Rapid IoT
- NXP Designs
- SafeAssure-Community
- OSS Security & Maintenance
- Using Our Community
-
- Cloud Lab Forums
-
- Knowledge Bases
- ARM Microcontrollers
- i.MX Processors
- Identification and Security
- Model-Based Design Toolbox (MBDT)
- QorIQ Processing Platforms
- S32 Automotive Processing Platform
- Wireless Connectivity
- CodeWarrior
- MCUXpresso Suite of Software and Tools
- MQX Software Solutions
-
- Home
- :
- MCUXpressoソフトウェアとツール
- :
- Kinetisデザインスタジオ
- :
- Re: How do you flash a chip with flash security enabled in your image?
How do you flash a chip with flash security enabled in your image?
- RSS フィードを購読する
- トピックを新着としてマーク
- トピックを既読としてマーク
- このトピックを現在のユーザーにフロートします
- ブックマーク
- 購読
- ミュート
- 印刷用ページ
- 新着としてマーク
- ブックマーク
- 購読
- ミュート
- RSS フィードを購読する
- ハイライト
- 印刷
- 不適切なコンテンツを報告
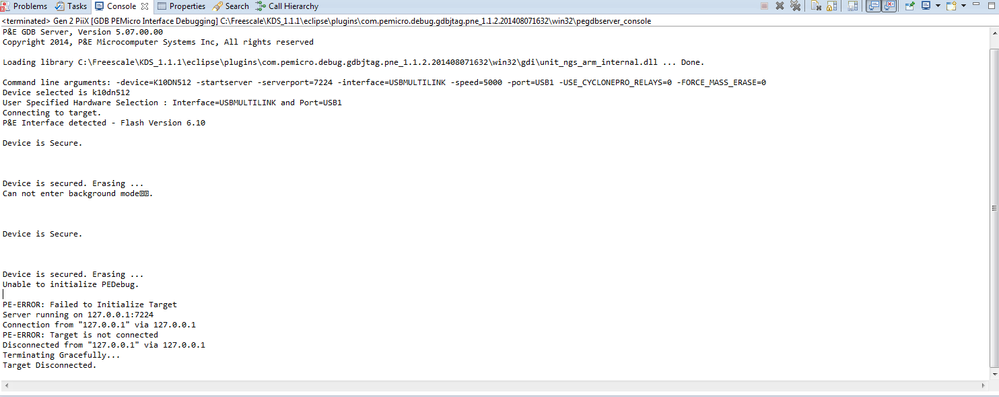
I turned on flash security in security settings of the cpu bean. Now when I try to flash or debug I get the following message:
Initializing.
Device is Secure.
Device is secured. Erasing ...
Target has been RESET and is active.
Disconnected from "127.0.0.1" via 127.0.0.1
Terminating Gracefully...
Target Disconnected.
It appears to be doing a mass erase and then disconnecting. No code appears to run, tested by setting an output pin at the beginning of main and it never gets set. When I recompile the code without the flash security bit, everything works, code runs as expected. Is there a way to set flash security and flash a chip with that setting?
Is there a better way to secure the firmware image?
解決済! 解決策の投稿を見る。
- 新着としてマーク
- ブックマーク
- 購読
- ミュート
- RSS フィードを購読する
- ハイライト
- 印刷
- 不適切なコンテンツを報告
Tried codewarrior but the mk22fn256 isn't supported. Ended up finding a way to flash a flash locked image with p&e:
Create a blank project in kds3.
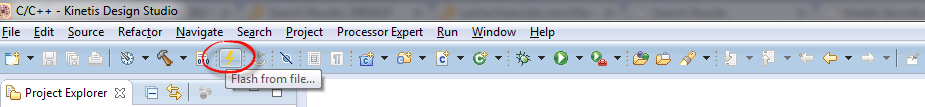
Use the flash icon instead of the debug icon.
Point it to the elf file from the kds1 project and click flash.
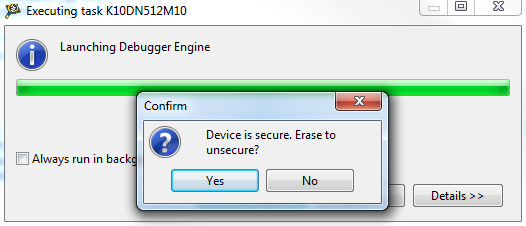
There will be 2 popups asking to erase or something, click no both times.
Wait for debugger to crash.
Power cycle device and it will run with the flash locked image.
- 新着としてマーク
- ブックマーク
- 購読
- ミュート
- RSS フィードを購読する
- ハイライト
- 印刷
- 不適切なコンテンツを報告
try in Code Warrior
- 新着としてマーク
- ブックマーク
- 購読
- ミュート
- RSS フィードを購読する
- ハイライト
- 印刷
- 不適切なコンテンツを報告
Tried codewarrior but the mk22fn256 isn't supported. Ended up finding a way to flash a flash locked image with p&e:
Create a blank project in kds3.
Use the flash icon instead of the debug icon.
Point it to the elf file from the kds1 project and click flash.
There will be 2 popups asking to erase or something, click no both times.
Wait for debugger to crash.
Power cycle device and it will run with the flash locked image.
- 新着としてマーク
- ブックマーク
- 購読
- ミュート
- RSS フィードを購読する
- ハイライト
- 印刷
- 不適切なコンテンツを報告
Hi Josh,
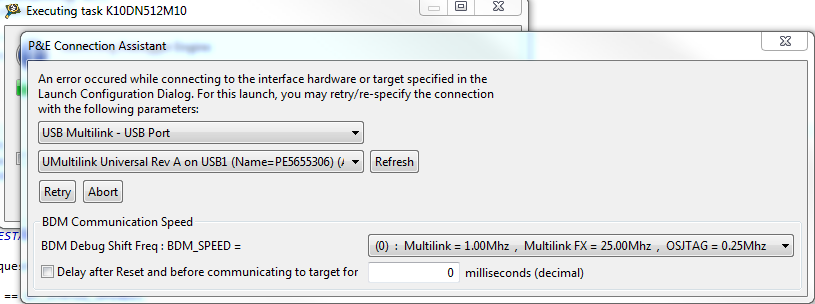
Which flash programmer are you using? is it a P&E multilink?
The behavior you are experiencing happens because when you use the Debugger to flash your device, it will perform the download to the device but then it will try to start the debug session and will notice that the device is secured, so the debugger will perform a mass erase on the device to unsecure it and be able to debug the code. I would recommended not to secure the device in the development phase of the project.
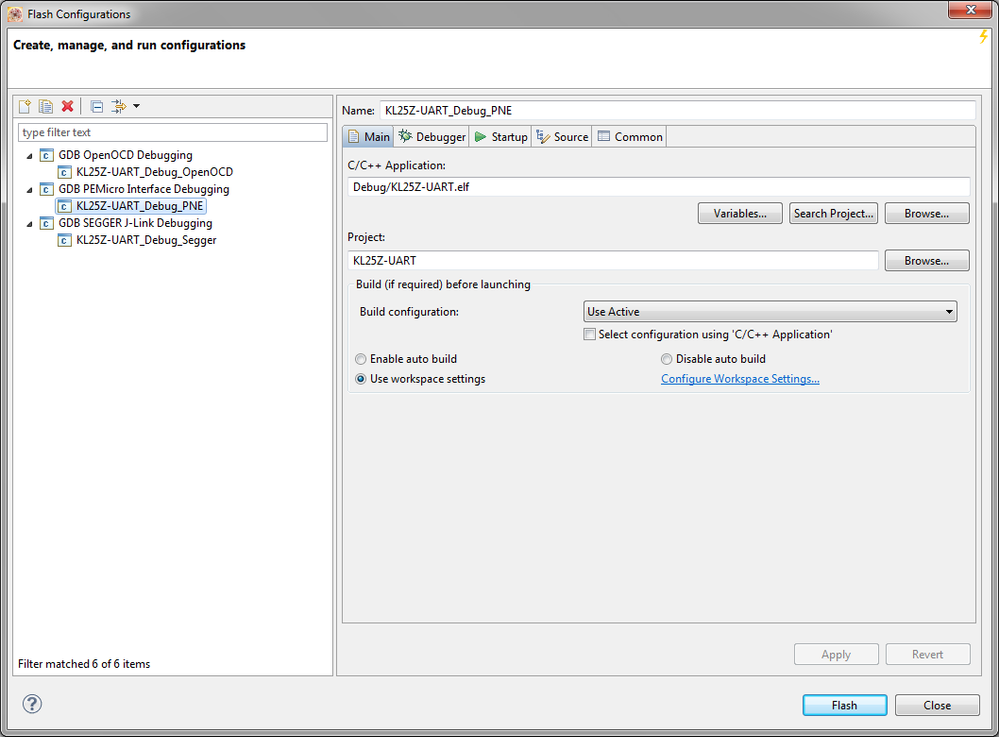
You can use the "Flash from file" utility in order to flash your device when the security is enabled :
After you click on it a window will show up where you can select the connection to use:
Hope it helps!
Best Regards,
Carlos Mendoza
Technical Support Engineer
-----------------------------------------------------------------------------------------------------------------------
Note: If this post answers your question, please click the Correct Answer button. Thank you!
-----------------------------------------------------------------------------------------------------------------------
- 新着としてマーク
- ブックマーク
- 購読
- ミュート
- RSS フィードを購読する
- ハイライト
- 印刷
- 不適切なコンテンツを報告
Hi Carlos,
I have an issue about the flash security enabled image.
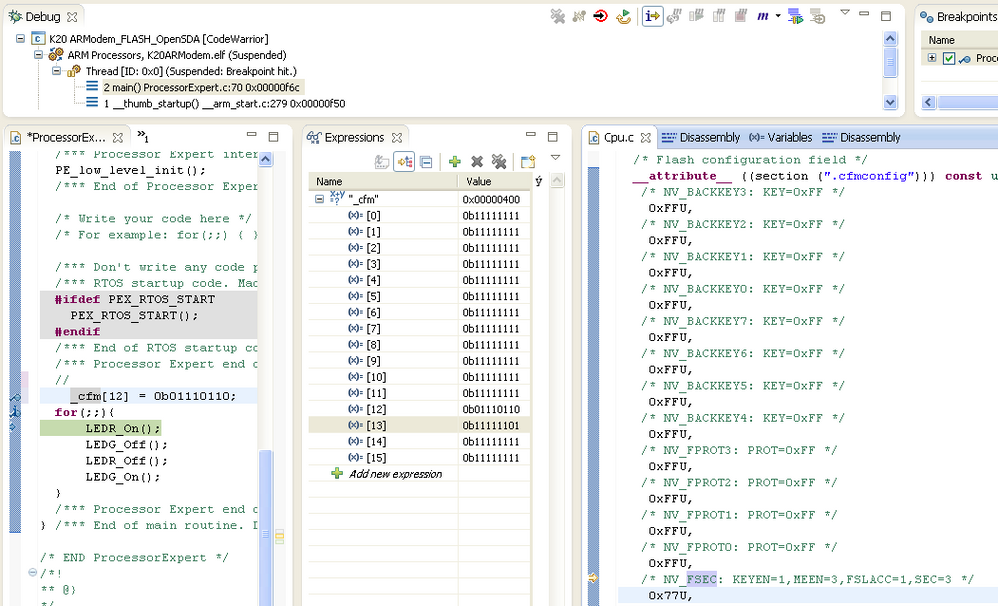
I had flashed the K10 with a security enabled image in Code Warrior 10.5 via P&E USB Multilink.
but after K10 is security enabled, I could not flash the K10 again neither with a security enabled iamge nor a security disabled image at all.
Under Code Warrior, there will be a popup window like below:
I click yes and this window popup again, I click yes again then the below window shows up saying some errors happen:
and i then tried to use debugger in KDS1.1.1, it shows the below information in the Console Tab:
So now i have no way to reflash the K10 any longer
Do you know why and what is the solution for me?
thank you!
- 新着としてマーク
- ブックマーク
- 購読
- ミュート
- RSS フィードを購読する
- ハイライト
- 印刷
- 不適切なコンテンツを報告
Hello Daniel!
Reading your issues sound like enabled flash security with mass erase disabled.
For get better understanding, maybe you need read this post How (not) to Secure my Microcontroller | MCU on Eclipse.
Regards!
- 新着としてマーク
- ブックマーク
- 購読
- ミュート
- RSS フィードを購読する
- ハイライト
- 印刷
- 不適切なコンテンツを報告
Hi Carlos
I think the mass erase is enabled in my image.
I have checked the s record file I am using, the MEEN bit is actually set to 3 which means the Mass erase is enabled
Here is the flash configuration line in the s record file I had flashed into K10
S214000400FFFFFFFFFFFFFFFFFFFFFFFF7CFBFFFF7E
You can see that the value of FTFL_FSEC is 0x7C
but the FTFL_FOPT is set to 0xFB, which means NMI_DIS is 0, is that safe?
and What would you suggest I can do to be able to reprogram the K10?
- 新着としてマーク
- ブックマーク
- 購読
- ミュート
- RSS フィードを購読する
- ハイライト
- 印刷
- 不適切なコンテンツを報告
Hello Daniel!
Don't matter if the MEEN record now is 11, if you downloaded the program at least one time is enough.
This document could help you.
Please if you discover what problem have you k10 MCU, please tell us.
Regards
- 新着としてマーク
- ブックマーク
- 購読
- ミュート
- RSS フィードを購読する
- ハイライト
- 印刷
- 不適切なコンテンツを報告
I'm using the P&E multilink. It appears that the flash tool does the same thing as the debug tool. Has the same options, same log messages. I don't see a way to stop it from trying to step thru code and erasing when it can't.
- 新着としてマーク
- ブックマーク
- 購読
- ミュート
- RSS フィードを購読する
- ハイライト
- 印刷
- 不適切なコンテンツを報告
Hello Josh and Scott,
I have done some test and the mcu cannot be secured using P&E multilink and KDS, this is because KDS does not have the feature to allow pop-up dialogs, because of this the user cannot be warned that the chip is secured and choose whether to erase the flash or disconnect from the debugger, so without the pop up it gets automatically erased.
If you want to secure the device you could use a J-Link programmer, with it you should be able to flash and secure the device using the "Flash from file" utility in KDS. Another option is to use CodeWarrior, the "Flash programmer" utility in CodeWarrior allows you to flash your device with security enabled using the P&E multilink programmer but maybe the device you are using is not supported on this IDE, please take a look to the supported devices here:
http://www.freescale.com/webapp/sps/site/prod_summary.jsp?code=CW-MCU10
Hope it helps!
Best Regards,
Carlos Mendoza
Technical Support Engineer
-----------------------------------------------------------------------------------------------------------------------
Note: If this post answers your question, please click the Correct Answer button. Thank you!
-----------------------------------------------------------------------------------------------------------------------
- 新着としてマーク
- ブックマーク
- 購読
- ミュート
- RSS フィードを購読する
- ハイライト
- 印刷
- 不適切なコンテンツを報告
Hello Carlos!
I'm using a FRDM-KL46Z and FRDM-K20D50M and enabling the security flash option on the "Component Inspector - CPU".
If I download the program with Flash File To Target choosing:
* The correct connection
* Flash configuration file: KL46Z256M4.xml
* The .elf of the program on file to flash
Clicking on "Erase and Program" the program downloads to the board and runs well after pressing the reset button... but when I try the attach option in debug mode, it allows me to debug as if the security flash option is disabled.
In the document "Using the Kinetis Security and Flash Protection Features" at FSEC field description says when "FSEC[SEC] = 01" the "MCU security status is secure" then the debug mode must be disabled, but I still can get access the debug mode, Do you know why?
- 新着としてマーク
- ブックマーク
- 購読
- ミュート
- RSS フィードを購読する
- ハイライト
- 印刷
- 不適切なコンテンツを報告
Thats bad news. We have a product we can't release until flash security can be verified.
- 新着としてマーク
- ブックマーク
- 購読
- ミュート
- RSS フィードを購読する
- ハイライト
- 印刷
- 不適切なコンテンツを報告
Hi Josh! The solution of this issues are explain in this thred called "Trouble with security flash on KL46Z".
- 新着としてマーク
- ブックマーク
- 購読
- ミュート
- RSS フィードを購読する
- ハイライト
- 印刷
- 不適切なコンテンツを報告
Greetings,
Just a note to add to Mr. Mendoza's correct analysis in that currently KDS is missing the popup dialogs when using P&E hardware interfaces. These dialogs will be put into the next build of KDS, whenever that may be. So it is important to keep up to date on the KDS version to get the latest features and bug fixes.
Takao Yamada
P&E MIcrocomputer Systems
- 新着としてマーク
- ブックマーク
- 購読
- ミュート
- RSS フィードを購読する
- ハイライト
- 印刷
- 不適切なコンテンツを報告
KDS3 with the P&E dialogs still fails to program an image that has flash lock compiled into it. The dialog comes up where it asks if you want to erase flash, and clicking yes causes the same thing to happen as in KDS1. It erases the chip and then tries to run on an erased chip. It never writes the image. When I disable flash lock and recompile it is able to flash the device without problems. We are aware that a jlink will work but we already spent a lot of money on a P&E device and feel that we shouldn't have to buy 2 expensive debuggers.
- 新着としてマーク
- ブックマーク
- 購読
- ミュート
- RSS フィードを購読する
- ハイライト
- 印刷
- 不適切なコンテンツを報告
Carlos -
We've have the same issue with KDS that Josh reported, and we have tried using the "Flash from file" option but it has the same problem. We're using KDS1.1.1 and we use a P&B USB Multilink.
How did you set up your configuration in order to get this to work for you?
Here's what the tail part of our Console looks like when doing the "Flash from file:" (I have trimmed some of the blank lines) and you can see it still does a mass erase.
CMD>PM
Programming.
Processing Object File Data ...
Programmed.
CMD>VC
Verifying object file CRC-16 to device ranges ...
block 00000000-000001DF ...
Ok.
block 00000400-0003957B ...
Ok.
Checksum Verification Successful. (Cumulative CRC-16=$7A8F)
CMD>RE
Initializing.
Device is Secure.
Device is secured. Erasing ...
Target has been RESET and is active.
Disconnected from "127.0.0.1" via 127.0.0.1
Terminating Gracefully...
Target Disconnected.