- Forums
- Product Forums
- General Purpose MicrocontrollersGeneral Purpose Microcontrollers
- i.MX Forumsi.MX Forums
- QorIQ Processing PlatformsQorIQ Processing Platforms
- Identification and SecurityIdentification and Security
- Power ManagementPower Management
- MCX Microcontrollers
- S32G
- S32K
- S32V
- MPC5xxx
- Other NXP Products
- Wireless Connectivity
- S12 / MagniV Microcontrollers
- Powertrain and Electrification Analog Drivers
- Sensors
- Vybrid Processors
- Digital Signal Controllers
- 8-bit Microcontrollers
- ColdFire/68K Microcontrollers and Processors
- PowerQUICC Processors
- OSBDM and TBDML
-
- Solution Forums
- Software Forums
- MCUXpresso Software and ToolsMCUXpresso Software and Tools
- CodeWarriorCodeWarrior
- MQX Software SolutionsMQX Software Solutions
- Model-Based Design Toolbox (MBDT)Model-Based Design Toolbox (MBDT)
- FreeMASTER
- eIQ Machine Learning Software
- Embedded Software and Tools Clinic
- S32 SDK
- S32 Design Studio
- GUI Guider
- Zephyr Project
- Voice Technology
- Application Software Packs
- Secure Provisioning SDK (SPSDK)
- Processor Expert Software
- MCUXpresso Training Hub
-
- Topics
- Mobile Robotics - Drones and RoversMobile Robotics - Drones and Rovers
- NXP Training ContentNXP Training Content
- University ProgramsUniversity Programs
- Rapid IoT
- NXP Designs
- SafeAssure-Community
- OSS Security & Maintenance
- Using Our Community
-
- Cloud Lab Forums
-
- Knowledge Bases
- ARM Microcontrollers
- i.MX Processors
- Identification and Security
- Model-Based Design Toolbox (MBDT)
- QorIQ Processing Platforms
- S32 Automotive Processing Platform
-
- Home
- :
- General Purpose Microcontrollers
- :
- Kinetis Microcontrollers
- :
- MKL13Z64 ROM bootloader app downloading?
MKL13Z64 ROM bootloader app downloading?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
MKL13Z64 ROM bootloader app downloading?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
I have tried to find the ROM bootloader service app for the MKL13Z64 mcu and couldn't find it. Could anybody please guide me to where I can download it?
Thanks!
Jieqiu
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Jieqiu,
About the KL13 app code, you can use our SDK, please go to this link:
https://mcuxpresso.nxp.com/en/select
Select the KL13Z64 chip, then generate the code and download it, you can use the IDE generate the .bin file at first.
About the ROM bootloader download, please refer to our KBOOT2.0:
Download the KBOOT2.0, then you refer to document: Getting Started with the Kinetis ROM Bootloader.pdf and Kinetis Bootloader Demo Application User's Guide.pdf in folder:
NXP_Kinetis_Bootloader_2_0_0\doc
Wish it helps you!
Have a great day,
Kerry
-----------------------------------------------------------------------------------------------------------------------
Note: If this post answers your question, please click the Correct Answer button. Thank you!
-----------------------------------------------------------------------------------------------------------------------
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Kerry,
Thank you for your quick reply.
Sorry I have got more questions. I am going to try the ROM bootloader. It seems that it can only be used when it is the first time to load the code. Once an app is in the flash, it will need to reset the boot root bit to boot the ROM bootloader. I haven’t got the board back yet.
If it is the case, I have to use a Flash-Resident Bootloader. Could you please advise me any available example code for this flash resident bootloader I can work on?
Cheers
Jieqiu
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Jieqiu,
Do you have the JLINK, and your KL03 have the reseved SWD interface?
If yes, please use the JLINK command, connect your chip, then input: unlock kinetis
Just to the mass erase.
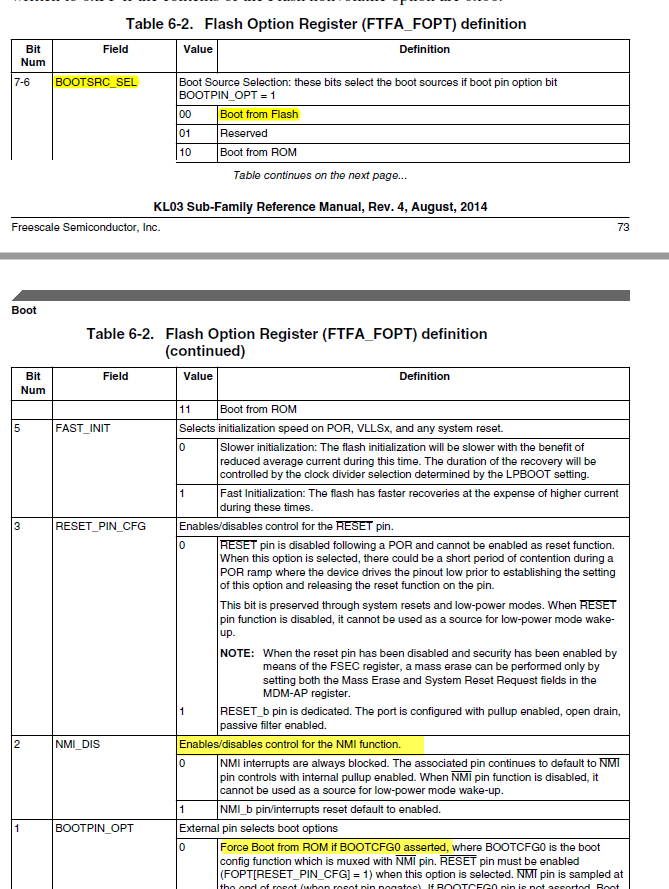
I am afraid the problem is caused by your app, it modified the FOPT in flash adddress 0X40D.
If you configure the chip boot from flash, and enable BOOTPIN_OPT, then you can't enter the ROM bootloader again, you must need to erase the flash configuration field, then you can enter ROM bootloader.
Anyway, use external debugger JLINK to do the mass erase at first.
Then check your application code, flash address 0x40d, what's the data in the FOPT?
Have a great day,
Kerry
-----------------------------------------------------------------------------------------------------------------------
Note: If this post answers your question, please click the Correct Answer button. Thank you!
-----------------------------------------------------------------------------------------------------------------------
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Kerry,
In this project, I am using MKL13Z64 MCU. Two questions:
1. Can I reconfigure the FOPT register in my app? What I try to do is that when reboot to ROM is needed, I can send a command to the app to reconfigure the FOPT register. Then when next reset occurs, the ROM bootloader can be booted. Is this possible?
2. Is it possible to get a flash resident bootloader?
Thanks
Jieqiu
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Jieqiu,
1. You can configure the FOPT register in your app, but now, the app already downloaded to your flash, you can't modify the FOPT with your downloaded app now. Do you tried the JLINK? You also can check the 0X40D data directly, I don't know what's you FOPT data now. If you want to use the app to reconfigure the FOPT after receiving the command, you can write the code to modify the FOPT in your app. You can copy the data to RAM at first, then erase the FOPT flash sector, write that sector again. Just do the flash operation in your app. But I think you don't need to do it, actually, in the app, you just leave the NMI to enter the ROM bootloader is OK.
2. Of course you can use flash bootloader, but KL13 already have the ROM bootloader, if you just use UART, USB, SPI bootloader, ect. you don't need to rewrite the flash bootloader, because you just have 64K flash.
Wish it helps you!
Have a great day,
Kerry
-----------------------------------------------------------------------------------------------------------------------
Note: If this post answers your question, please click the Correct Answer button. Thank you!
-----------------------------------------------------------------------------------------------------------------------