- Forums
- Product Forums
- General Purpose MicrocontrollersGeneral Purpose Microcontrollers
- i.MX Forumsi.MX Forums
- QorIQ Processing PlatformsQorIQ Processing Platforms
- Identification and SecurityIdentification and Security
- Power ManagementPower Management
- Wireless ConnectivityWireless Connectivity
- RFID / NFCRFID / NFC
- Advanced AnalogAdvanced Analog
- Neural Processing UnitsNeural Processing Units
- MCX Microcontrollers
- S32G
- S32K
- S32V
- MPC5xxx
- Other NXP Products
- S12 / MagniV Microcontrollers
- Powertrain and Electrification Analog Drivers
- Sensors
- Vybrid Processors
- Digital Signal Controllers
- 8-bit Microcontrollers
- ColdFire/68K Microcontrollers and Processors
- PowerQUICC Processors
- OSBDM and TBDML
- S32M
- S32Z/E
-
- Solution Forums
- Software Forums
- MCUXpresso Software and ToolsMCUXpresso Software and Tools
- CodeWarriorCodeWarrior
- MQX Software SolutionsMQX Software Solutions
- Model-Based Design Toolbox (MBDT)Model-Based Design Toolbox (MBDT)
- FreeMASTER
- eIQ Machine Learning Software
- Embedded Software and Tools Clinic
- S32 SDK
- S32 Design Studio
- GUI Guider
- Zephyr Project
- Voice Technology
- Application Software Packs
- Secure Provisioning SDK (SPSDK)
- Processor Expert Software
- Generative AI & LLMs
-
- Topics
- Mobile Robotics - Drones and RoversMobile Robotics - Drones and Rovers
- NXP Training ContentNXP Training Content
- University ProgramsUniversity Programs
- Rapid IoT
- NXP Designs
- SafeAssure-Community
- OSS Security & Maintenance
- Using Our Community
-
- Cloud Lab Forums
-
- Knowledge Bases
- ARM Microcontrollers
- i.MX Processors
- Identification and Security
- Model-Based Design Toolbox (MBDT)
- QorIQ Processing Platforms
- S32 Automotive Processing Platform
- Wireless Connectivity
- CodeWarrior
- MCUXpresso Suite of Software and Tools
- MQX Software Solutions
- RFID / NFC
- Advanced Analog
- Neural Processing Units
-
- NXP Tech Blogs
- Home
- :
- MCUXpresso Software and Tools
- :
- MCU Bootloader
- :
- KL03 ROM bootloader inconsistent behavior
KL03 ROM bootloader inconsistent behavior
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi there,
I'm running the ROM bootloader of the MKL03Z32VFK4 and noticed something very weird. The first time I run the "blhost --usb --buspal i2c -d flash-erase-all-unsecure" command, it fails, but the second time it succeeds.
1st blhost invocation:
$ blhost --usb --buspal i2c -d flash-erase-all-unsecure
Inject pre-config command 'i2c'
[01 00 0c 00 c1 00 00 02 10 00 00 00 64 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00]
<03 00 0c 00 a0 00 00 02 00 00 00 00 c1 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00>
Successful generic response to command 'i2c'
- took 0.000 seconds
Response status = 0 (0x0) Success.
Inject command 'flash-erase-all-unsecure'
[01 00 04 00 0d 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00]
<03 00 00 00 0d 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00>
usbhid: received data phase abort
<>
sendCommandGetResponse.readPacket error 5.
processResponse: null packet
- took 0.000 seconds
Response status = 10004 (0x2714) No response packet from target device.
2nd blhost invocation:
$ blhost --usb --buspal i2c -d flash-erase-all-unsecure
Inject pre-config command 'i2c'
[01 00 0c 00 c1 00 00 02 10 00 00 00 64 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00]
<03 00 0c 00 a0 00 00 02 00 00 00 00 c1 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00>
Successful generic response to command 'i2c'
- took 0.000 seconds
Response status = 0 (0x0) Success.
Inject command 'flash-erase-all-unsecure'
[01 00 04 00 0d 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00]
<03 00 0c 00 a0 00 00 02 00 00 00 00 0d 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00>
Successful generic response to command 'flash-erase-all-unsecure'
- took 0.000 seconds
Response status = 0 (0x0) Success.
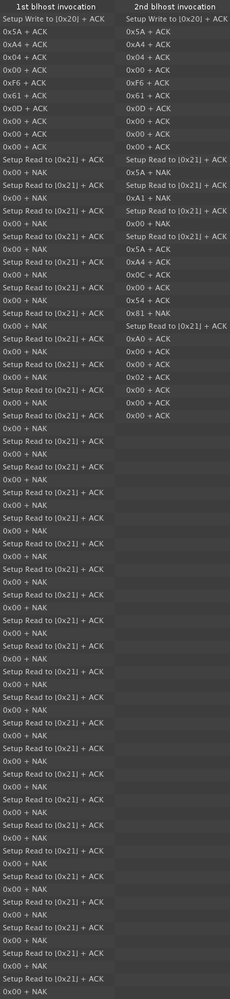
I've put the I2C protocol dump of the first and second blhost invocations side by side. Please note that the first invocation is directly followed by the second invocation. There is no extra communication in between.
According to the above, the KL03 ROM bootloader fails to answer the first invocation but works perfectly for the second invocation. Upon subsequent calls, this pattern continues:
- KL03 ROM bootloader starts up
- blhost --usb --buspal i2c -d flash-erase-all-unsecure -> FAIL
- blhost --usb --buspal i2c -d flash-erase-all-unsecure -> SUCCESS
- blhost --usb --buspal i2c -d flash-erase-all-unsecure -> FAIL
- blhost --usb --buspal i2c -d flash-erase-all-unsecure -> SUCCESS
- blhost --usb --buspal i2c -d flash-erase-all-unsecure -> FAIL
- blhost --usb --buspal i2c -d flash-erase-all-unsecure -> SUCCESS
- ...
Lastly, I must also note that I had to add 2 lines of code to BusPal to go this far. Without the extra read that I added, it always fails because it considers the extra 0 byte that the bootloader sends part of the framing packet. According to the protocol documentation, "0x00 will be sent as the response to host if the target is busy with processing or
preparing data", so it seems to be legit, but it's a bit strange that it's always sent, even when the communication speed is set to 1kHz in which case the bootloader should have plenty of time to do processing.
Please somebody explain the above to me. I need the bootloader to behave consistently, and I cannot give any meaningful explanation other than the KL03 ROM bootloader is buggy.
Thanks!
- Laci
Solved! Go to Solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mr. Santiago J. González Fabián has just let me know about errata ID 8060 which is the likely culprit here. Looks like I will have to explicitly retry to work around this bug. Thanks a ton, Santiago!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Mr. Santiago J. González Fabián has just let me know about errata ID 8060 which is the likely culprit here. Looks like I will have to explicitly retry to work around this bug. Thanks a ton, Santiago!