- NXP Forums
- Product Forums
- General Purpose MicrocontrollersGeneral Purpose Microcontrollers
- i.MX Forumsi.MX Forums
- QorIQ Processing PlatformsQorIQ Processing Platforms
- Identification and SecurityIdentification and Security
- Power ManagementPower Management
- MCX Microcontrollers
- S32G
- S32K
- S32V
- MPC5xxx
- Other NXP Products
- Wireless Connectivity
- S12 / MagniV Microcontrollers
- Powertrain and Electrification Analog Drivers
- Sensors
- Vybrid Processors
- Digital Signal Controllers
- 8-bit Microcontrollers
- ColdFire/68K Microcontrollers and Processors
- PowerQUICC Processors
- OSBDM and TBDML
-
- Solution Forums
- Software Forums
- MCUXpresso Software and ToolsMCUXpresso Software and Tools
- CodeWarriorCodeWarrior
- MQX Software SolutionsMQX Software Solutions
- Model-Based Design Toolbox (MBDT)Model-Based Design Toolbox (MBDT)
- FreeMASTER
- eIQ Machine Learning Software
- Embedded Software and Tools Clinic
- S32 SDK
- S32 Design Studio
- Vigiles
- GUI Guider
- Zephyr Project
- Voice Technology
- Application Software Packs
- Secure Provisioning SDK (SPSDK)
- Processor Expert Software
-
- Topics
- Mobile Robotics - Drones and RoversMobile Robotics - Drones and Rovers
- NXP Training ContentNXP Training Content
- University ProgramsUniversity Programs
- Rapid IoT
- NXP Designs
- SafeAssure-Community
- OSS Security & Maintenance
- Using Our Community
-
-
- Home
- :
- General Purpose Microcontrollers
- :
- LPC Microcontrollers
- :
- secure boot
secure boot
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
secure boot
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
I use secure boot as follows:
1、Generate four sets of certificates;serial number field of image certificates :3C:C3:00:00:AB:AB:AB:AB
2、with elftosb_gui, config load address to be 0x10000000; elftosb_gui show “Verifysignature ” is "success".
3、load this signed image;
4、config "Version" of CFPA to 0x01 and config "ROTKH_REVOKE"为0x55; CFPA is attached;
5、config ROTKH of CMPA with RKTH generated by elftosb_gui;config SECURE_BOOT_CFG of CMPA to 0x40000000(signed image); DIGEST of CMPA is not configed。
after reset, the image is not right running。 why?
Can you provide an available certificate? I suspect there is something wrong with my certificate。
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
hello,Alice:
OpenSSL I haven't yet configured successfully,so certificates are generated by a tool found online; I'm trying to configure OpenSSL. Certificate in SDK expired and elftosb reported an error,Is it possible to provide a certificate?
other question, DIGEST of CMPA is not configed,secure boot is configed; Is there any other way to modify CMPA except bootloader.
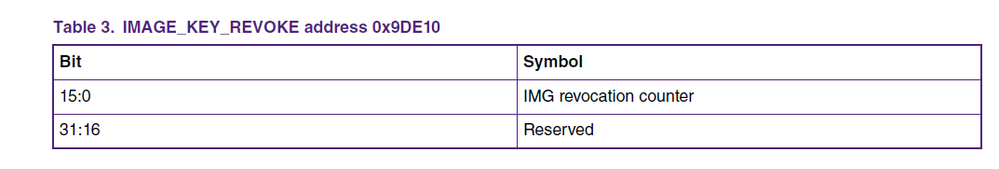
I find that IMAGE_KEY_REVOKE of CFPA has 4 bytes from address 0x9DE10, but it only need two bytes; so i shall write 3C C3 00 00 from address 0x9DE10 ?
Can you provide an example of a complete set of operational processes? What is the first step?What is the second step? ...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello ning xie,
About the steps, please refer to this Application Note:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello,Alice:
Thank you very much for your reply;The following three questions can be answered:
1、OpenSSL I haven't yet configured successfully,so certificates are generated by a tool found online; I'm trying to configure OpenSSL. Certificate in SDK expired and elftosb reported an error,Is it possible to provide a certificate?
2、 DIGEST of CMPA is not configed,secure boot is configed; Is there any other way to modify CMPA except bootloader.
3、 I find that IMAGE_KEY_REVOKE of CFPA has 4 bytes from address 0x9DE10, but it only need two bytes; so i shall write 3C C3 00 00 from address 0x9DE10 ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello ning xie,
1. Sorry I can't give you a certificate, as I also need give you the Key. What's the problem when you using OpenSSL?
2. About this question, I will help you ask development team whether this is method.
3. From AN12283 we can see, in IMAGE_KEY_REVOKE, the 31:16 reserved, only two bytes (15:0) are used as
IMG revocation counter:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello,Alice:
Thank you very much for your reply;When I use boot, I do the following:
Data preparation process:
1、I generated a secure image with a starting address of 0x10000000, the size of this image is 0x10424; config of this image :load address(0x10000000) 、imageTZ-M Enable but no preset data、add four ROOT keys, key is generated by referring to AN12283_LPC55Sxx_Secure_boot; As an annex“elftosb_gui”
The starting address of the non secure code is 0x20000, no crc 、no signed;
2、CFPA:config "Version" of CFPA to 0x01 and config "ROTKH_REVOKE"为0x55;As an annex“cfpa_9DE00_1.bin”
3、CMPA is generated using elftosb_gui tool: SECURE_BOOT_CFG(0x9E41C) is Boot signed images、
RKTH is generated using elftosb tools(01747922a5d76949d3db0b7eb1cce7cfce9a46516456b19ea78f53375af2b943)、
DIGEST also is generated using elftosb tools.As an annex“cmpa_9E400_1.bin”
note: puf、prince are not used.
Operating process:
1、 Enter boot,erase flash :blhost.exe -p COM45 -- flash-erase-region 0x00000 0x40000;
2、load image:blhost -p COM45 write-memory 0x20000 hello_world_ns_0614.bin 、blhost -p COM45 write-memory 0 hello_world_s_sig_0614.bin;
3、read and write CFPA :
blhost -p COM45 read-memory 0x9DE00 512 cfpa_9DE00_0.bin
blhost -p COM45 read-memory 0x9E000 512 cfpa_9E000_0.bin
blhost -p COM45 read-memory 0x9E200 512 cfpa_9E200_0.bin
blhost -p COM45 write-memory 0x9DE00 cfpa_9DE00_1.bin
blhost -p COM45 read-memory 0x9DE00 512 cfpa_9DE00_2.bin
blhost -p COM45 read-memory 0x9E000 512 cfpa_9E000_2.bin
blhost -p COM45 read-memory 0x9E200 512 cfpa_9E200_2.bin
4、read and write CMPA :
blhost -p COM45 read-memory 0x9E400 512 cmpa_9E400_0.bin
blhost -V -p COM45,57600 -- write-memory 0x9E400 cmpa_9E400_1.bin
5、reset,Running error;
these steps are right ? Looking forward to your reply.