- Forums
- Product Forums
- General Purpose MicrocontrollersGeneral Purpose Microcontrollers
- i.MX Forumsi.MX Forums
- QorIQ Processing PlatformsQorIQ Processing Platforms
- Identification and SecurityIdentification and Security
- Power ManagementPower Management
- Wireless ConnectivityWireless Connectivity
- RFID / NFCRFID / NFC
- Advanced AnalogAdvanced Analog
- Neural Processing UnitsNeural Processing Units
- MCX Microcontrollers
- S32G
- S32K
- S32V
- MPC5xxx
- Other NXP Products
- S12 / MagniV Microcontrollers
- Powertrain and Electrification Analog Drivers
- Sensors
- Vybrid Processors
- Digital Signal Controllers
- 8-bit Microcontrollers
- ColdFire/68K Microcontrollers and Processors
- PowerQUICC Processors
- OSBDM and TBDML
- S32M
- S32Z/E
-
- Solution Forums
- Software Forums
- MCUXpresso Software and ToolsMCUXpresso Software and Tools
- CodeWarriorCodeWarrior
- MQX Software SolutionsMQX Software Solutions
- Model-Based Design Toolbox (MBDT)Model-Based Design Toolbox (MBDT)
- FreeMASTER
- eIQ Machine Learning Software
- Embedded Software and Tools Clinic
- S32 SDK
- S32 Design Studio
- GUI Guider
- Zephyr Project
- Voice Technology
- Application Software Packs
- Secure Provisioning SDK (SPSDK)
- Processor Expert Software
- Generative AI & LLMs
-
- Topics
- Mobile Robotics - Drones and RoversMobile Robotics - Drones and Rovers
- NXP Training ContentNXP Training Content
- University ProgramsUniversity Programs
- Rapid IoT
- NXP Designs
- SafeAssure-Community
- OSS Security & Maintenance
- Using Our Community
-
- Cloud Lab Forums
-
- Knowledge Bases
- ARM Microcontrollers
- i.MX Processors
- Identification and Security
- Model-Based Design Toolbox (MBDT)
- QorIQ Processing Platforms
- S32 Automotive Processing Platform
- Wireless Connectivity
- CodeWarrior
- MCUXpresso Suite of Software and Tools
- MQX Software Solutions
- RFID / NFC
- Advanced Analog
- Neural Processing Units
-
- NXP Tech Blogs
- Home
- :
- RFID / NFC
- :
- NFC Knowledge Base
- :
- Mifare Ultralight C - Changing default password and protecting page address
Mifare Ultralight C - Changing default password and protecting page address
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Mifare Ultralight C - Changing default password and protecting page address
Mifare Ultralight C - Changing default password and protecting page address
Hello NFC community,
MIFARE® Ultralight-based tickets offer an ideal solution for low-cost, high-volume applications such as public transport, loyalty cards and event ticketing. They serve as a perfect contactless replacement for magnetic stripe, barcode, or QR-code systems. The introduction of the contactless MIFARE Ultralight® ICs for limited-use applications can lead to reduced system installation and maintenance costs. As you may know the MIFARE family has the Ultralight C tag which is a contactless IC supporting 3DES cryptography is mostly used in limited use applications such smart ticketing, this tag complies with ISO 14443-3 type A and it is defined as type 2 tag, in this document I want to show you the procedure to change the default key to a custom key also to protect certain areas in the tag so the authentication is needed to perform a read or write operation.
---------------------------------------------------------------------------------------------------
For this document I used :
- MFEV710: PEGODA Contactless Smart Card Reader
- RFIDDiscover Software
- Lite version
- Full Version Available in Docstore
- Mifare Ultralight c
---------------------------------------------------------------------------------------------------
Information
- Old Key : 49454D4B41455242214E4143554F5946
- New Key : 88776655443322117766554433221199
- Data sheet
----------------------------------------------------------------------------------------------------
- First we start with the procedure to activate the tag and the anticollision procedure explained in the ISO/IEC 14443-3.
Command Direction
- ">" this direction is command send from PCD (Reader) to PICC(Ultralight c)
- "<" this direction is command send from PICC (Ultralight c) to PCD (Reader)
- "=" Prepare this command before sending
Command |
| Data message |
REQA = Request Command, Type A | > | 26 |
ATQA = Answer To Request, Type A | < | 4400 |
SEL + NVB = SEL (Select code for cascade level ) 93, NVB (Number of Valid bits) 20 | > | 9320 |
ANTICOLLISION START | < | 8804598356 |
| > | 93708804598356 |
SAK (Select Acknowledge) = indicates additional cascade level | < | x04 |
| > | 9520 |
| < | E1ED2580A9 |
| > | 9570E1ED2580A9 |
| < | x00 |
UID = 045983E1ED2580
** the following procedure is explained in section 7.5.5 from the datasheet**
Command |
| Data message |
Authenticate Part 1 (command 1A) | > | 1A00 |
| < | AFA1ED1D682E5101422CC7 |
Authenticate Part 2 (command AF) | > | AF2970D895F186D0302970D895F186D030188AAF4DAF68C5B9 |
| < | 006BD027CEC3E04EBC6919 |
[AUTHENTICATED]
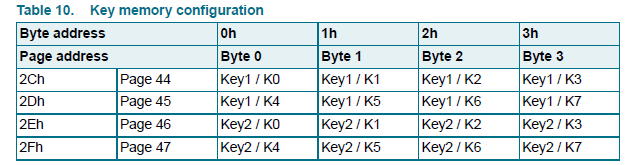
Then according to section 7.5.7 of the datasheet the sections where the 3DES key are saved are the 2C (Page 44) to the 2F (Page 47).
We proceed to write our new key using the A2 (WRITE command)
Command |
| Data message |
DATA = byte 07,06,05,04 | = | 11223344 |
WRITE to page 44 (2C) | > | A22C11223344 |
Positive acknowledge (ACK) | < | 0A |
DATA = byte 03,02,01,00 | = | 55667788 |
WRITE to page 45 (2D) | > | A22D55667788 |
Positive acknowledge (ACK) | < | 0A |
DATA = byte 0F,0E,0D,0C | = | 99112233 |
WRITE to page 46 (2E) | > | A22E99112233 |
Positive acknowledge (ACK) | < | 0A |
DATA = byte 0B,0A,09,08 | = | 44556677 |
WRITE to page 47 (2F) | > | A22F44556677 |
Positive acknowledge (ACK) | < | 0A |
[RESET FIELD]
[Authenticate with new key]
Command |
| Data message |
Authenticate Part 1 (command 1A | > | 1A00 |
| < | AFFAE2EFF17FAAD69862E7 |
Authenticate Part 2 (command AF) | > | AFFD5794F2D4EA1B19FD5794F2D4EA1B196CF420CD4D9E8104 |
| < | 0030922228601939B8FA18 |
[AUTENTICATED WITH NEW KEY]
we proceed to define from which sector the authentication is needed in order to read or write, to do this we use a write command to the AUTH0 (AUTH0 defines the page address from which the authentication is required. Valid address values for byte AUTH0 are from 03h to 30h.)
the AUTH0 is located on the section 2A please check table 5 from #datasheet.
**for this example we will define that from page 6 (06) we will need authentication to perform a read or write operation**
Command |
| Data message |
WRITE command (A2) to AUTH0 (2A) from page 6 (06) | > | A22A06000000 |
Positive acknowledge (ACK) | < | 0A |
Now the Read capabilities from page 06 require an Authentication in order to be read or written.
Hope you find this document useful to get a better understanding of the behavior of the Ultralight C and how its security features can help you in your applications.
Have a great day!
BR
Jonathan