- NXP Forums
- Product Forums
- General Purpose MicrocontrollersGeneral Purpose Microcontrollers
- i.MX Forumsi.MX Forums
- QorIQ Processing PlatformsQorIQ Processing Platforms
- Identification and SecurityIdentification and Security
- Power ManagementPower Management
- MCX Microcontrollers
- S32G
- S32K
- S32V
- MPC5xxx
- Other NXP Products
- Wireless Connectivity
- S12 / MagniV Microcontrollers
- Powertrain and Electrification Analog Drivers
- Sensors
- Vybrid Processors
- Digital Signal Controllers
- 8-bit Microcontrollers
- ColdFire/68K Microcontrollers and Processors
- PowerQUICC Processors
- OSBDM and TBDML
-
- Solution Forums
- Software Forums
- MCUXpresso Software and ToolsMCUXpresso Software and Tools
- CodeWarriorCodeWarrior
- MQX Software SolutionsMQX Software Solutions
- Model-Based Design Toolbox (MBDT)Model-Based Design Toolbox (MBDT)
- FreeMASTER
- eIQ Machine Learning Software
- Embedded Software and Tools Clinic
- S32 SDK
- S32 Design Studio
- Vigiles
- GUI Guider
- Zephyr Project
- Voice Technology
- Application Software Packs
- Secure Provisioning SDK (SPSDK)
- Processor Expert Software
-
- Topics
- Mobile Robotics - Drones and RoversMobile Robotics - Drones and Rovers
- NXP Training ContentNXP Training Content
- University ProgramsUniversity Programs
- Rapid IoT
- NXP Designs
- SafeAssure-Community
- OSS Security & Maintenance
- Using Our Community
-
-
- Home
- :
- Product Forums
- :
- Wireless Connectivity Knowledge Base
- :
- USB-KW41 Bluetooth LE Sniffer Application Update
USB-KW41 Bluetooth LE Sniffer Application Update
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
USB-KW41 Bluetooth LE Sniffer Application Update
USB-KW41 Bluetooth LE Sniffer Application Update
This document describes how to update and sniff Bluetooth LE wireless applications on the USB-KW41
Programming the USB-KW41 as sniffer
It was noticed that there are some issues trying to follow a Bluetooth LE connection, even if the sniffer catches the connection request. These issues have been fixed in the latest binary file which can be found in the Test Tool for Connectivity Products 12.8.0.0 or newest.
After the Test Tool Installation, you’ll find the sniffer binary file at the following path.
C:\NXP\Test Tool 12.8.1.0\images\KW41_802.15.4_SnifferOnUSB.bin
Programming Process.
1. Connect the USB-KW41Z to your PC, and it will be enumerated as Mass Storage Device
2. Drag and drop the "KW41_802.15.4_SnifferOnUSB.bin" included in Test tool for Connectivity Products.
"C:\NXP\Test Tool 12.8.0.0\images\KW41_802.15.4_SnifferOnUSB.bin"
3. Unplug the device and hold the RESET button of the USB-KW41Z, plug to your PC and the K22 will enter in bootloader mode.
4. Drag and drop the "sniffer_usbkw41z_k22f_0x8000.bin" included in Test tool for Connectivity Products.
"C:\NXP\Test Tool 12.8.5.9\images\sniffer_usbkw41z_k22f_0x8000.bin"
5. Then, unplug and plug the USB-KW41Z to your PC.
Note: If the USB-KW41 is not enumerated as Mass Storage Device, please look at the next thread https://community.nxp.com/thread/444708
General Recommendations
Software Tools
Hardware Tools
-
1 USB-KW41 (updated with KW41_802.15.4_SnifferOnUSB.bin from Test Tool 12.8 or later)
The Kinetis Protocol Analyzer provides the ability to monitor the Bluetooth LE Advertisement Channels. It listens to all the activity and follows the connection when capturing a Connection Request.
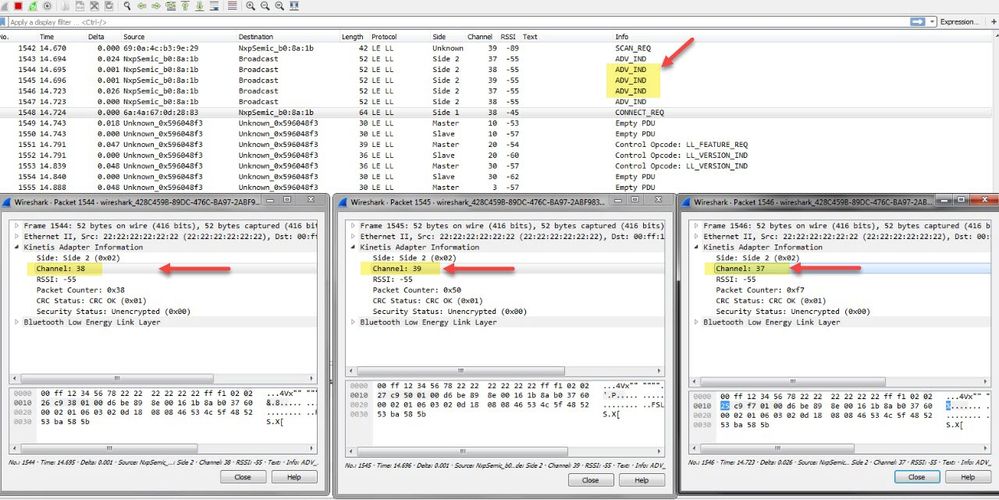
Bluetooth LE Peripheral device transmits packets on the 3 advertising channels one after the other, so the USB-KW41 will listen to the 3 channels one by one and could or not catch the connection request.
Common use case
The USB-KW41 will follow the Bluetooth LE connection if the connection request happens on the same channel that It is listening. If is listening to a different channel when the connection request is sent, it won't be able to follow it.
A Simple recommendation is the Bluetooth LE Peripheral should be set up to send the adv packets only to one channel and the sniffer just capturing on the same channel.
Improvement
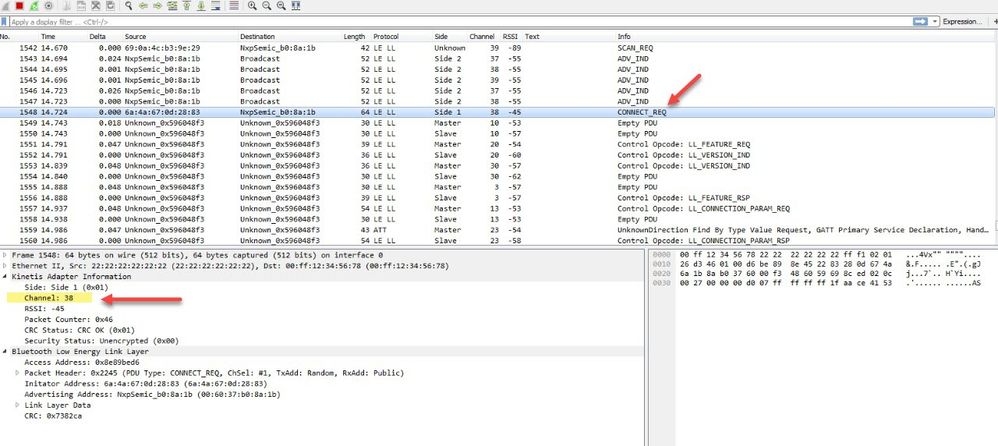
Use 3 USB-KW41, each of them will be dedicated to one channel and will catch the connection request.
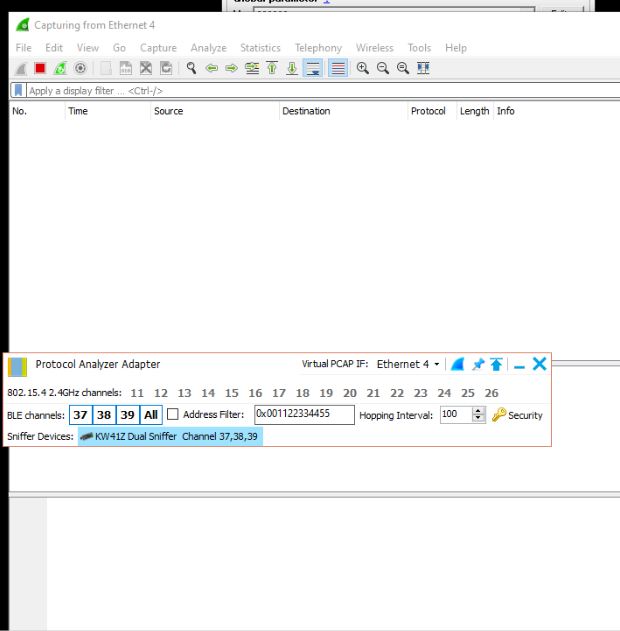
Configure Kinetis Protocol Analyzer and Wireshark Network Analyzer
Note: For better results, address filter can be activated.
When you are capturing all the packets in the air, you will notice 3 adv packets. Each packet will show the adv channel that is getting the adv frame.
One of the three sniffers will capture the Connection Request. In this case, it happens on channel 38.
You will be able to follow the connection, see all the data exchange.
For a better reference, you can look at the USB-KW41 Getting Started
Hope it helps
Regards,
Mario
- Mark as Read
- Mark as New
- Bookmark
- Permalink
- Report Inappropriate Content
I followed your steps and programmed the USB dongle as sniffer as mentioned above, but in the end, when I'm opening Wireshark from Protocol analyzer adapter tool, there is nothing captured, even tested with a scanner and there are 2 advertisers in the room. How can I identify the problem? is there any log to check?
Thank you in advance!
Regards,
Nicu